7. Managing the Greenbone Operating System¶
Note
This chapter documents all possible menu options.
However, not all GSM types support all of these menu options. Check the tables in Chapter 3 to see whether a specific feature is available for the used GSM type.
7.1. General Information¶
7.1.1. Greenbone Security Feed (GSF) Subscription Key¶
When purchasing a Greenbone Security Manager (GSM), a unique Greenbone Security Feed (GSF) subscription key is pre-installed to grant the GSM access to the Greenbone Update Service, also called the Greenbone Feed Service. The subscription key is used for authorization purposes only, not for billing or encryption.
The subscription key is individual for each GSM and cannot be installed on more than one GSM appliance.
If the subscription key is compromised (e.g., gets into the hands of third parties), no damage will occur for the rightful owner of the subscription key. Greenbone Networks will deactivate the compromised key, preventing further unauthorized use. A replacement subscription key may be issued at no cost.
A factory reset will delete the subscription key from the GSM and the subscription key has to be re-installed. If a factory reset is planned, contact the Greenbone Networks Support via e-mail (support@greenbone.net) to receive a copy of the subscription key.
7.1.2. Authorization Concept¶
The GSM offers two different levels of access:
- Web Interface/GMP – User Level
- The user level is available via the web interface or the Greenbone Management Protocol (GMP).
- GOS Administration Menu – System Level
- The system level is only available via console or secure shell protocol (SSH).
7.1.2.1. User Level Access¶
The user level provides access to the vulnerability scanning and vulnerability management functionalities and supports the administration of users, groups and detailed permissions.
Accessing the user level is possible either via the web interface, also called Greenbone Security Assistant (GSA), or via Greenbone Management Protocol (GMP).
Note
For the GSM types GSM 35 and GSM 25V, no user level access is supported. These appliances have to be managed using a GSM master.
When the GSM is delivered by Greenbone Networks or after a factory reset, no user level account is configured on the GSM. It is necessary to create at least one such account via the system level.
7.1.2.2. System Level Access¶
The system level provides access to the administration of the Greenbone Operating System (GOS). Only a single system administrator account is supported. The system administrator cannot modify system files directly but can instruct the system to change configurations.
GOS is managed using a menu-based graphical interface (GOS administration menu). The system administrator is not required to use the command line (shell) for configuration or maintenance tasks. Shell access is provided for support and troubleshooting purposes only.
Accessing the system level requires either console access (serial, hypervisor or monitor/keyboard) or a connection via SSH. To use SSH, a network connection is required and the SSH service has to be enabled (see Chapter 7.2.3.3).
When the GSM is delivered by Greenbone Networks or after a factory reset, a default system administrator account and password is pre-configured. During the initial setup the system administrator password should be changed (see Chapter 7.2.1.1).
7.1.2.2.1. Accessing the GOS Administration Menu Using the Console¶
Once turned on, the appliance boots. The boot process can be monitored via the console.
After the boot process is completed, the login prompt is shown (see Fig. 7.1). The default login information is:
- user:
admin - password:
admin
Note
During the first setup this password should be changed (see Chapter 7.2.1.1).
When the GSM is delivered by Greenbone Networks or after a factory reset, a setup wizard is shown after the login to assist with the basic configuration of GOS. By selecting Yes and pressing Enter all mandatory settings can be configured. By selecting No or Cancel and pressing Enter the setup wizard is closed.
7.1.2.2.2. Accessing the GOS Administration Menu Using SSH¶
Note
When the GSM is delivered by Greenbone Networks or after a factory reset, SSH access may be deactivated and has to be enabled first using the console (see Chapter 7.2.3.3). A network connection is required for SSH as well (see Chapter 7.2.2.2).
To establish a SSH connection on Linux, macOS or Unix-like systems, the command line can be used as follows:
$ ssh admin@<gsm>
Replace <gsm> with the IP address or domain name of the GSM appliance.
The host key can be verified by displaying its fingerprint as follows:
Start the GOS administration menu.
Select Setup and press Enter.
Select Services and press Enter.
Select SSH and press Enter.
Select Fingerprint and press Enter.
→ The fingerprint is displayed on the GOS administration menu.
To establish an SSH connection on Microsoft Windows systems, the tools PuTTY or smarTTY can be used. On Microsoft Windows Server 2019, Microsoft Windows 10 Build 1809, or newer, the OpenSSH Client component can be installed to access SSH via the command line.
7.1.3. Using the GOS Administration Menu¶
The GOS administration menu can be navigated using a keyboard. The arrow keys of the keyboard can be used to move the current menu selection. Pressing Enter is used to confirm the current menu selection and to continue. Pressing Space is used to toggle on/off switches. The current menu can be exited by pressing Esc.
Configuration changes made in the GOS administration menu are not activated immediately. Instead, the menu option Save is added below the other options (see Fig. 7.2). The changes take effect by selecting Save and pressing Enter.
If a menu is exited without saving the outstanding changes, a warning is displayed (see Fig. 7.3). The changes can be saved by selecting Yes and pressing Enter. If No is selected, the changes are discarded.
7.2. Setup Menu¶
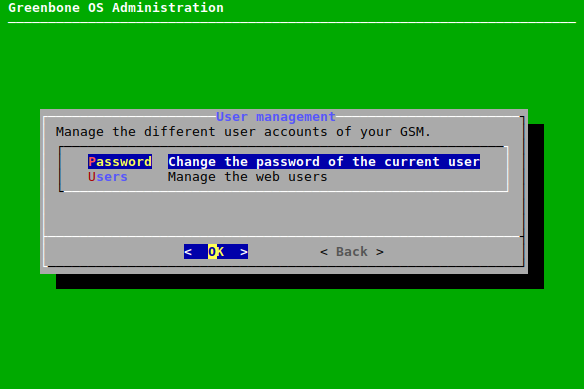
7.2.1. Managing Users¶
The GOS administration menu offers the possibility to manage web users. Web users are the users of the web interface of the GSM.
7.2.1.1. Changing the System Administrator Password¶
The password of the system administrator can be changed. This is especially important during the first base configuration. The factory setting is not suitable for a production environment. The password can be changed as follows:
Select Setup and press Enter.
Select User and press Enter.
Select Password and press Enter (see Fig. 7.4).
Enter the current password and press Enter (see Fig. 7.5).
Enter the new password and press Enter.
Note
Trivial passwords are rejected. This includes the default password
adminas well.Repeat the new password and press Enter.
Note
The change is effective immediately and a commit of the change is not required. A rollback is not possible either.
7.2.1.2. Managing Web Users¶
Note
There are no web users for the GSM types GSM 35 and GSM 25V.
For these GSM types, this chapter is not relevant.
To be able to use the GSM appliance a web administrator must be set up. This user is being referred to as scan administrator in some documentation and by some applications.
The set-up of the first web administrator is only possible using the GOS administration menu as follows:
Select Setup and press Enter.
Select User and press Enter.
Select Users and press Enter.
→ Several new options are displayed (see Fig. 7.6).
Select List Users and press Enter to display a list of all configured web users.
Note
More than one user with administrative rights can be set up.
To edit the existing users, or add users with fewer permissions, the web interface has to be used.
7.2.1.3. Creating a Web Administrator¶
A web administrator can be created as follows:
Select Setup and press Enter.
Select User and press Enter.
Select Users and press Enter.
Select Admin User and press Enter.
Determine the user name and the password of the web administrator and press Tab (see Fig. 7.7).
Press Enter.
→ The web administrator is created and can be edited in the web interface.
7.2.1.4. Enabling a Guest User¶
To allow a guest to log in without needing a password, this feature has to be activated as follows:
Select Setup and press Enter.
Select User and press Enter.
Select Users and press Enter.
Select Guest User and press Enter.
Enter the user name and the password of an existing user and press Tab.
Press Enter.
→ The guest user is enabled and can log in to the web interface without needing the password (see Fig. 7.8).
7.2.1.5. Creating a Super Administrator¶
A super administrator can be created as follows:
Select Setup and press Enter.
Select User and press Enter.
Select Users and press Enter.
Select Super Admin and press Enter.
→ A warning asks to confirm the process (see Fig. 7.9).
Select Yes and press Enter.
Determine the user name and the password of the super administrator and press Tab.
Press Enter.
→ The super administrator is created and can be edited in the web interface.
Note
The super administrator can only be edited by the super administrator.
7.2.1.6. Deleting a User Account¶
A web user can be deleted as follows:
Select Setup and press Enter.
Select User and press Enter.
Select Users and press Enter.
Select Delete Account and press Enter.
Select the web user that should be deleted and press Enter.
Note
The web user is deleted immediately.
Press Enter to return to the previous menu.
7.2.1.7. Changing a User Password¶
The password of a web user can be changed as follows:
Select Setup and press Enter.
Select User and press Enter.
Select Users and press Enter.
Select Change Password and press Enter.
Select the web user of which the password should be changed and press Enter.
Enter the new password twice and press Tab (see Fig. 7.10).
Press Enter.
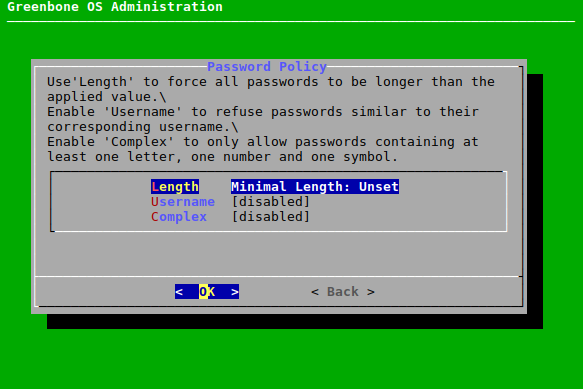
7.2.1.8. Changing the Password Policy¶
The requirements for passwords can be changed as follows:
Select Setup and press Enter.
Select User and press Enter.
Select Users and press Enter.
Select Password Policy and press Enter.
Select Length and press Enter to set the minimal length a password must have.
Select Username and press Enter to determine whether user name and password can be the same.
Select Complex and press Enter to determine whether a password has to contain at least one letter, one number and one symbol.
7.2.2. Configuring the Network Settings¶
Note
Any change within the network configuration has to be saved in the menu and the GSM has to be rebooted for the change to be fully effective.
Some GSM types (GSM 5400/6500 and GSM 400/450/600/650) have two different namespaces:
- Namespace: Management
- This namespace includes all interfaces required for management activities.
- Namespace: Scan1
- This namespace includes all interfaces required for scanning purposes.
By default, all interfaces are in the management namespace. This enables both management and scan traffic on all interfaces. As soon as at least one interface is in the scan namespace, namespace separation goes into effect.
Only interfaces in the management namespace can handle management traffic. This includes accessing the GOS administration menu, the web interface, the Greenbone Feed Server and configuring the master-sensor communication.
Only interfaces in the scan namespace can handle scan traffic.
The namespaces are separated to connect only the interfaces in the scan namespace to networks accessible from the internet. In that way, attacks from the internet cannot reach the management interfaces of the GSM.
Tip
Separating the namespaces is recommended.
7.2.2.1. Switching an Interface to Another Namespace¶
Interfaces that should be in namespace scan1 can be selected as follows:
Select Setup and press Enter.
Select Network and press Enter.
Select Configure Namespaces and press Enter.
→ The namespace scan1 is selected.
Press Enter.
Select the desired interface that should be switched to the namespace scan1 and press Space.
→ The interface is marked with *. Interfaces that are in the management namespace are labeled accordingly (see Fig. 7.12).
Press Enter.
7.2.2.2. Configuring Network Interfaces¶
Note
At least one network interface must be configured to access the GSM using the network. Usually the first network adapter eth0 is used for this. The administrator has to configure this network interface and to attach the appliance to the network.
Depending on the GSM type the first network interface is preconfigured:
- GSM ONE: DHCP
- All other GSM types: no IP address set
By default, IPv6 is disabled on all GSM types.
Network interfaces can be configured as follows:
Select Setup and press Enter.
Select Network and press Enter.
Select the namespace of the desired interface and press Enter.
Select Interfaces and press Enter.
Select the desired interface and press Enter.
Note
If there is only one interface in this namespace, the configuration of the interface is opened directly.
→ The interface can be configured (see Fig. 7.13).
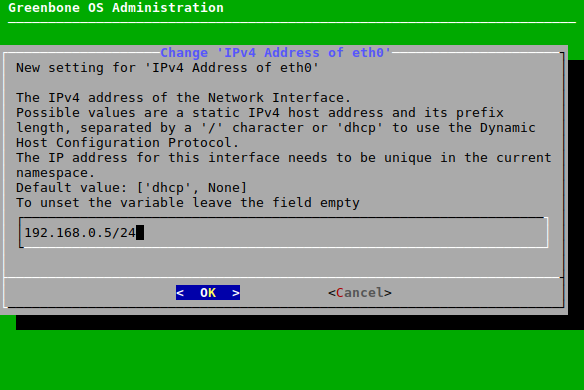
7.2.2.2.1. Setting up a Static IP Address¶
Select the desired interface (see Chapter 7.2.2.2).
Select Static IP (for IPv4 or IPv6) and press Enter.
Delete
dhcpfrom the input box and replace it with the correct IP address including the prefix length (see Fig. 7.14).Press Enter.
→ A message informs that the changes have to be saved (see Chapter 7.1.3).
Press Enter to close the message.
Note
The static IP can be disabled by leaving the input box empty.
7.2.2.2.2. Configuring a Network Interface to Use DHCP¶
A network interface can be configured to use DHCP as follows:
- Select the desired interface (see Chapter 7.2.2.2).
- Select DHCP (for IPv4 or IPv6) and press Enter.
7.2.2.2.3. Configuring the Maximum Transmission Unit (MTU)¶
Note
The configuration of the MTU is only possible if a static IP address is configured.
Select the desired interface (see Chapter 7.2.2.2).
Select MTU (for IPv4 or IPv6) and press Enter.
Enter the MTU in the input box.
Press Enter.
→ A message informs that the changes have to be saved (see Chapter 7.1.3).
Press Enter to close the message.
Note
If the input box is left empty, the default value is set.
7.2.2.2.4. Using the Router Advertisement for IPv6¶
If the configuration of IP addresses and the routing for IPv6 should be performed automatically, router advertisement can be enabled as follows:
- Select the desired interface (see Chapter 7.2.2.2).
- Select Router-advertisement and press Enter.
7.2.2.2.5. Configuring VLANs¶
Note
VLAN interfaces are currently not supported on virtual appliances. If the hypervisor supports virtual switches, this can be used to realize the functionality.
A new VLAN subinterface can be created as follows:
Select the desired interface (see Chapter 7.2.2.2).
Select Configure the VLAN interfaces on this interface and press Enter.
Select Configure a new VLAN interface and press Enter.
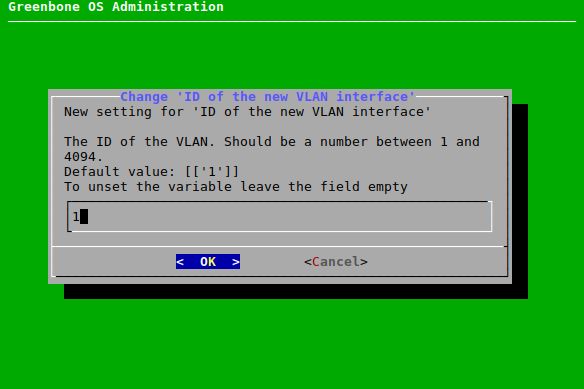
Enter the VLAN ID in the input box and press Enter (see Fig. 7.15).
→ A message informs that the changes have to be saved (see Chapter 7.1.3).
Press Enter to close the message.
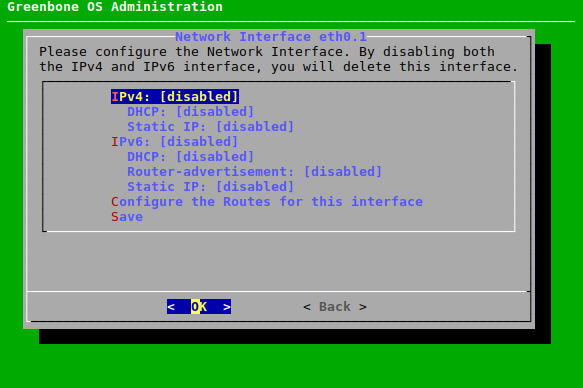
→ The new interface can be configured using IPv4 and IPv6 (see Fig. 7.16).
All created subinterfaces can be configured as follows:
7.2.2.2.6. Configuring the Routes for an Interface¶
A new route for an interface can be configured as follows:
Select the desired interface (see Chapter 7.2.2.2).
Select Configure the Routes for this interface and press Enter.
Select Configure IPv4 Routes or Configure IPv6 Routes and press Enter (see Fig. 7.17).
Select Add a new route and press Enter.
Enter the target network and the next hop in the input boxes, select OK and press Enter.
All created routes can be configured as follows:
- Select the desired interface (see Chapter 7.2.2.2).
- Select Configure the Routes for this interface and press Enter.
- Select Configure IPv4 Routes or Configure IPv6 Routes and press Enter.
- Select the desired route and press Enter.
- Edit the route, select OK and press Enter.
7.2.2.3. Configuring the DNS Server¶
For receiving the feed and updates, the GSM requires a reachable and functioning DNS (Domain Name System) server for name resolution. This setting is not required if the GSM uses a proxy for downloading the feed and updates.
If DHCP is used for the configuration of the network interfaces, the DNS servers provided by the DHCP protocol are used.
The GSM supports up to three DNS servers. At least one DNS server is required. Additional servers will only be used if an outage of the first server occurs.
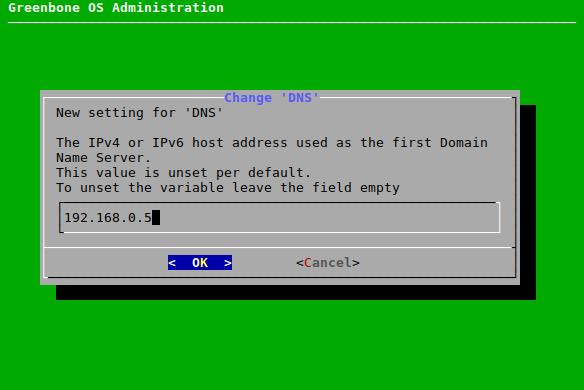
The DNS server can be configured as follows:
Select Setup and press Enter.
Select Network and press Enter.
Select Namespace: Management and press Enter.
Select DNS and press Enter.
Select the desired DNS server and press Enter.
Enter the IP address used as the DNS server in the input box and press Enter (see Fig. 7.18).
→ A message informs that the changes have to be saved (see Chapter 7.1.3).
Press Enter to close the message.
Note
Whether the DNS server can be reached and is functional can be determined by performing a selfcheck (see Chapter 7.3.1).
7.2.2.4. Configuring the Global Gateway¶
The global gateway may be obtained automatically using DHCP or router advertisements. The global gateway is often called the default gateway as well.
Note
If the GSM is configured to use static IP addresses, the global gateway has to be configured manually. Separate options are available for IPv4 and IPv6.
If using DHCP to assign IP addresses, the global gateway will be set via DHCP unless the global gateway has been set explicitly.
The global gateway can be configured as follows:
Select Setup and press Enter.
Select Network and press Enter.
Select the namespace for which the global gateway should be configured and press Enter.
Select Global Gateway for IPv4 or Global Gateway (IPv6) for IPv6 and press Enter.
Select the desired interface and press Enter (see Fig. 7.19).
Enter the IP address used as the global gateway in the input box and press Enter.
→ A message informs that the changes have to be saved (see Chapter 7.1.3).
Press Enter to close the message.
7.2.2.5. Setting the Host Name and the Domain Name¶
While the GSM does not require a special host name, the host name is an important item when creating certificates and sending e-mails.
The host name is used to configure the short host name and the domain name option is used for the domain suffix. The factory default values are:
- Host name: gsm
- Domain name: gbuser.net
The host name and the domain name can be configured as follows:
Select Setup and press Enter.
Select Network and press Enter.
Select Namespace: Management and press Enter.
Select Hostname or Domainname and press Enter.
Enter the host name or the domain name in the input box and press Enter (see Fig. 7.20).
→ A message informs that the changes have to be saved (see Chapter 7.1.3).
Press Enter to close the message.
7.2.2.6. Restricting the Management Access¶
The IP address on which the management interface is available can be set.
All administrative access (SSH, HTTPS, GMP) will be restricted to the respective interface and will not be available on the other interfaces.
Note
This feature overlaps with the separation of namespaces (see Chapter 7.2.2). Separating the namespaces is recommended.
Note
If no IP address is set, the management interface will be available on all IP addresses of interfaces in the management namespace.
The IP address for the management interface can be set as follows:
Select Setup and press Enter.
Select Network and press Enter.
Select Namespace: Management and press Enter.
Select Management IP (v4) or Management IP (v6) and press Enter.
Enter the IP address for the management interface in the input box and press Enter (see Fig. 7.21).
Note
The IP address has to be the IP address of one of the interfaces in the management namespace. If another IP address is set, the management interface will not be available.
Either the IP address or the name of the interface (e.g.,
eth0) can be entered.
7.2.2.7. Displaying the MAC and IP Addresses and the Network Routes¶
The used MAC addresses, the currently configured IP addresses and the network routes of the GSM can be displayed in a simple overview.
Note
This does not support the configuration of the MAC addresses.
The MAC and IP addresses of the interfaces or network routes can be displayed as follows:
Select Setup and press Enter.
Select Network and press Enter.
Select the namespace for which the IP addresses, MAC addresses or network routes should be displayed and press Enter.
Select MAC, IP or Routes and press Enter.
→ The MAC/IP addresses or the network routes of the selected namespace are displayed (see Fig. 7.22).
7.2.3. Configuring Services¶
To access the GSM appliance remotely, many interfaces are available:
- HTTPS
- The web interface is the usual option for the creation, execution and analysis of vulnerability scans. It is activated by default and cannot be deactivated.
- GMP (Greenbone Management Protocol)
GMP allows for the communication with other Greenbone Networks products (e.g., an additional GSM). It is required for the master-sensor communication (see Chapter 16).
It can also be used for the communication of in-house software with the appliance (see Chapter 15).
- SSH
- SSH allows to access the GOS administration menu of the GSM. This access is deactivated by default and must be activated first, e.g., by using the serial console. Additionally, SSH is required for feed updates from the Greenbone Feed Server and for the master-sensor communication (see Chapter 16).
- SNMP
- SNMP read access of the GSM is possible via SNMPv3 (see Chapter 7.2.3.4).
7.2.3.1. Configuring HTTPS¶
7.2.3.1.1. Configuring the Timeout of the Web Interface¶
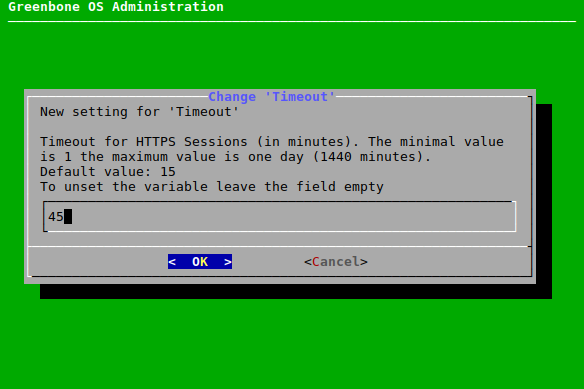
The timeout value of the web interface can be set as follows:
Select Setup and press Enter.
Select Services and press Enter.
Select HTTPS and press Enter.
Select Timeout and press Enter.
Enter the desired value for the timeout in the input box and press Enter
Note
The value can be between 1 and 1440 minutes (1 day). The default is 15 minutes.
→ A message informs that the changes have to be saved (see Chapter 7.1.3).
Press Enter to close the message.
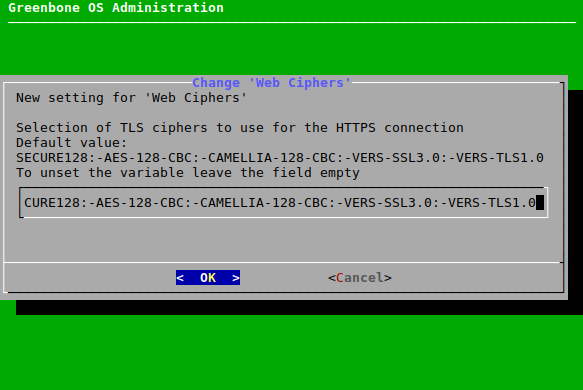
7.2.3.1.2. Configuring the Ciphers¶
The HTTPS ciphers can be configured. The current setting allows only secure ciphers using at least 128 bit key length, explicitly disallowing AES-128-CBC, Camellia-128-CBC and the cipher suites used by SSLv3 and TLSv1.0.
Select Setup and press Enter.
Select Services and press Enter.
Select HTTPS and press Enter.
Select Ciphers and press Enter.
Enter the desired value in the input box and press Enter (see Fig. 7.24).
Note
The string used to define the ciphers is validated by GnuTLS and must comply with the syntax “GnuTLS Priority Strings”. More information about the syntax can be found at https://gnutls.org/manual/html_node/Priority-Strings.html.
→ A message informs that the changes have to be saved (see Chapter 7.1.3).
Press Enter to close the message.
7.2.3.1.3. Managing Certificates¶
The GSM appliance basically uses two types of certificates:
- Self-signed certificates
- Certificates issued by an external CA
All modern operating systems support the creation and management of their own CA. Under Microsoft Windows Server the Active Directory Certificate Services support the administrator in the creation of a root CA. For Linux systems various options are available. One option is described in the IPSec-Howto.
When creating and exchanging certificates it needs to be considered that the administrator verifies how the systems are accessed later before creating the certificate. The IP address or the DNS name is stored when creating the certificate. Additionally, after creating the certificate a reboot is required so that all services can use the new certificate. This needs to be taken into consideration when changing certificates.
The current certificate can be displayed as follows:
Select Setup and press Enter.
Select Services and press Enter.
Select HTTPS and press Enter.
Select Certificate and press Enter.
Select Show and press Enter.
→ The certificte is displayed.
7.2.3.1.3.1. Self-Signed Certificates¶
The use of self-signed certificates is the easiest way. It poses, however, the lowest security and more work for the user:
- The trustworthiness of a self-signed certificate can only be checked manually by the user through importing the certificate and examining its fingerprint.
- Self-signed certificates cannot be revoked. Once they are accepted by the user, they are stored permanently in the browser. If an attacker gains access to the corresponding private key a man-in-the-middle attack on the connection protected by the certificate can be launched.
To support a quick setup, the GSM supports self-signed certificates. For most GSM types, such a certificate is not installed by default and must be created by the administrator. The GSM ONE, however, already comes with a pre-installed certificate.
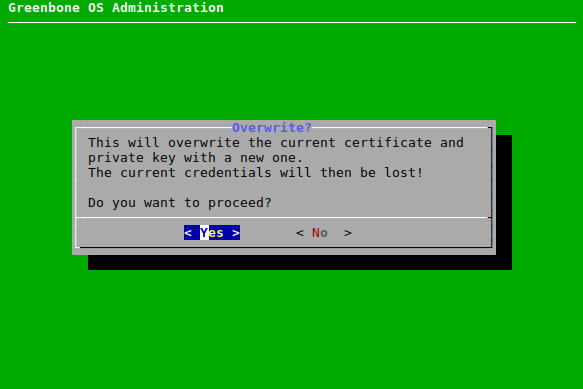
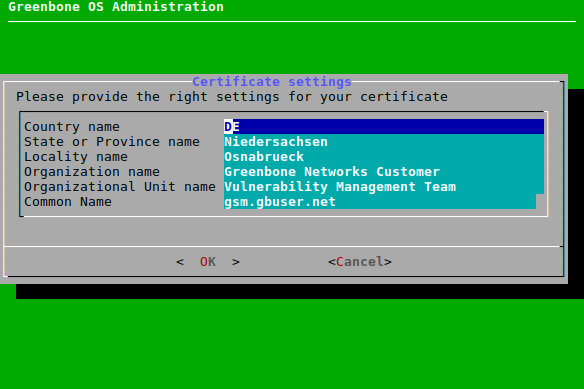
Self-signed certificates can be easily created as follows:
Select Setup and press Enter.
Select Services and press Enter.
Select HTTPS and press Enter.
Select Certificate and press Enter.
Select Generate and press Enter.
→ A message informs that the current certificate and private key will be overwritten (see Fig. 7.25).
Confirm the message by selecting Yes and pressing Enter.
Provide the settings for the certificate, select OK and press Enter.
→ When the process is finished, a message informs that the certificate can be downloaded.
Press Enter to close the message.
Select Download and press Enter.
Open the web browser and enter the displayed URL.
Download the PEM file.
In the GOS administration menu press Enter.
→ When the certificate is retrieved by the GSM, the GOS administration menu displays the fingerprint of the certificate for verification.
Check the fingerprint and confirm the certificate by pressing Enter.
→ To enable the new certificate a Reboot of the GSM is required (see Chapter 7.3.8.1).
7.2.3.1.3.2. Certificate by an External Certificate Authority (CA)¶
The use of a certificate issued by a CA has several advantages:
- All clients trusting the authority can verify the certificate directly and establish a security connection. No warning is displayed in the browser.
- The certificate can be revoked easily by the CA. If the clients have the ability to check the certificate status they can decline a certificate that may still be within its validity period but has been revoked. As mechanisms the Certificate Revocation Lists (CRLs) or Online Certificate Status Protocol (OCSP) can be used.
- Especially if multiple systems within an organization serve SSL/TLS protected information, the use of an organizational CA simplifies the management drastically. All clients simply have to trust the organizational CA to accept all the certificates issued by the CA.
To import a certificate by an external CA two options are available:
- Generate a certificate signing request (CSR) on the GSM, sign it using an external CA and import the certificate.
- Generate a CSR and the certificate externally and import both using a PKCS#12 file.
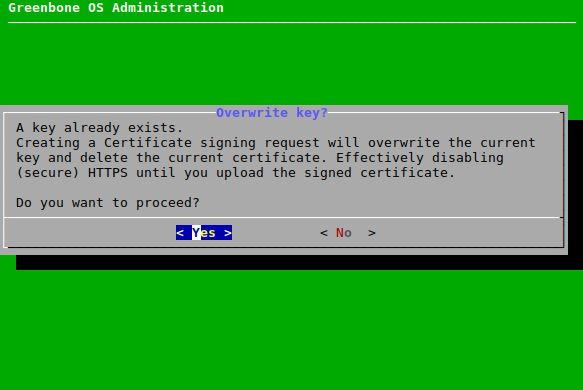
A new CSR can be created and the certificate can be imported as follows:
Select Setup and press Enter.
Select Services and press Enter.
Select HTTPS and press Enter.
Select Certificate and press Enter.
Select CSR and press Enter.
→ A message informs that the current certificate and private key will be overwritten (see Fig. 7.26).
Confirm the message by selecting Yes and pressing Enter.
Provide the settings for the certificate, select OK and press Enter.
Open the web browser and enter the displayed URL.
Download the PEM file.
→ The GOS administration menu displays a message to verify that the CSR has not been tampered with.
Verify the information by pressing Enter.
When the certificate is signed, select Certificate and press Enter.
Open the web browser and enter the displayed URL.
Click Browse…, select the signed certificate and click Upload.
→ When the certificate is retrieved by the GSM, the GOS administration menu displays the fingerprint of the certificate for verification.
Check the fingerprint and confirm the certificate by pressing Enter.
→ To enable the new certificate a Reboot of the GSM is required (see Chapter 7.3.8.1).
If a private key and a signed certificate which should be used for the GSM are already available, they can be imported. The private key and the certificate need to be formatted as a PKCS#12 file. The file can be protected using an export password.
The PKCS#12 file can be imported as follows:
Select Setup and press Enter.
Select Services and press Enter.
Select HTTPS and press Enter.
Select Certificate and press Enter.
Select PKCS#12 and press Enter.
→ A message informs that the current certificate and private key will be overwritten.
Confirm the message by selecting Yes and pressing Enter.
Open the web browser and enter the displayed URL.
Click Browse…, select the PKCS#12 container and click Upload.
Note
If an export password was used to protect the PKCS#12 container, the password has to be entered.
→ When the certificate is retrieved by the GSM, the GOS administration menu displays the fingerprint of the certificate for verification.
Check the fingerprint and confirm the certificate by pressing Enter.
→ To enable the new certificate a Reboot of the GSM is required (see Chapter 7.3.8.1).
7.2.3.1.4. Displaying Fingerprints¶
The fingerprints of the used certificate can be checked and displayed as follows:
Select Setup and press Enter.
Select Services and press Enter.
Select HTTPS and press Enter.
Select Fingerprints and press Enter.
→ The following fingerprints of the currently active certificate are displayed:
- SHA1
- SHA256
- BB
7.2.3.2. Configuring the Greenbone Management Protocol (GMP)¶
The Greenbone Management Protocol (GMP) can be activated using the GOS administration menu as follows:
Note
The SSH service has to be enabled before GMP can be enabled (see Chapter 7.2.3.3).
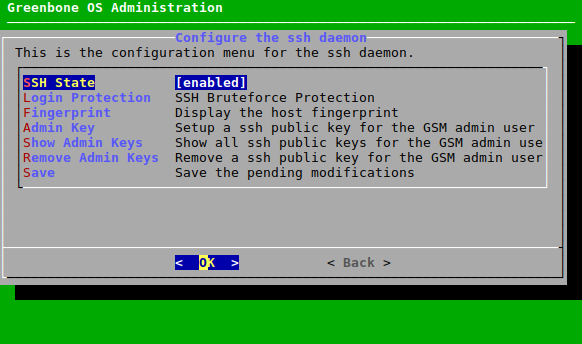
7.2.3.3. Configuring SSH¶
7.2.3.3.1. Enabling the SSH State¶
The SSH server embedded in the GSM can be enabled in the GOS administration menu as follows:
- Select Setup and press Enter.
- Select Services and press Enter.
- Select SSH and press Enter.
- Select SSH State and press Enter to enable SSH.
7.2.3.3.2. Enabling and Managing a Login Protection¶
A login protection can be enabled. If a number of consecutive login attempts fail, the user will be locked.
Note
The login protection does not block logging in via SSH admin key if such a key is set up (see Chapter 7.2.3.3.3).
The login protection can be enabled and managed as follows:
Select Setup and press Enter.
Select Services and press Enter.
Select SSH and press Enter.
Select Login Protection and press Enter.
Select Login Protection and press Enter (see Fig. 7.29).
→ A message informs that the login protection can lead to a locked SSH access.
Select Continue and press Enter to enable the login protection.
Select Login Attempts and press Enter.
Enter the desired value and press Enter.
→ A message informs that the changes have to be saved (see Chapter 7.1.3).
Press Enter to close the message.
In case the system is locked after too many failed login attempts, it has to be unlocked using console access (serial, hypervisor or monitor/keyboard) as follows:
Select Setup and press Enter.
Select User and press Enter.
Select Unlock SSH and press Enter.
→ The login attempt counter is reset.
Press Enter to close the message.
7.2.3.3.3. Adding an SSH Admin Key¶
SSH public keys can be uploaded to enable key-based authentication of administrators.
Note
SSH keys can be generated with OpenSSH by using the command ssh-keygen on Linux or puttygen.exe if using PuTTY on Microsoft Windows.
The formats Ed25519 or RSA are supported.
All SSH keys must correspond to RFC 4716.
An SSH admin key can be uploaded as follows:
Select Setup and press Enter.
Select Services and press Enter.
Select SSH and press Enter.
Select Admin Key and press Enter.
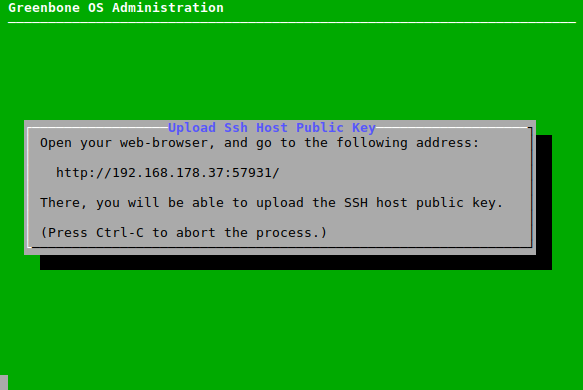
Open the web browser and enter the displayed URL (see Fig. 7.30).
Click Browse…, select the SSH public key and click Upload.
→ When the upload is completed, a message informs that the login via SSH is possible.
7.2.3.3.4. Displaying Fingerprints¶
The GSM provides different host keys for its own authentication. The client decides which public key to use. In the GOS administration menu the fingerprint of the public keys used by the SSH server of the appliance can be displayed as follows:
Select Setup and press Enter.
Select Services and press Enter.
Select SSH and press Enter.
Select Fingerprint and press Enter.
→ The SHA256 fingerprints of the following keys are displayed:
- ED25519
- RSA
7.2.3.4. Configuring SNMP¶
The GSM appliance supports SNMP. The SNMP support can be used for sending traps through alerts and monitoring of vital parameters of the appliance.
The supported parameters are specified in a Management Information Base (MIB) file. The current MIB is available from the Greenbone Tech-Doc-Portal.
The GSM supports SNMPv3 for read access and SNMPv1 for traps.
The SNMPv3 can be configured as follows:
Select Setup and press Enter.
Select Services and press Enter.
Select SNMP and press Enter.
Select SNMP and press Enter to enable SNMP.
→ Several new options are displayed (see Fig. 7.31).
Select Location and press Enter.
Enter the location of the SNMP service in the input box and press Enter.
Select Contact and press Enter.
Enter the contact of the SNMP service in the input box and press Enter.
Select Username and press Enter.
Enter the SNMP user name in the input box and press Enter.
Note
When configuring the authentication and privacy passphrase be aware of the fact that the GSM uses SHA-1 and AES128 respectively.
Select Authentication and press Enter.
Enter the SNMP user authentication passphrase in the input box and press Enter.
Select Privacy and press Enter.
Enter the SNMP user privacy passphrase in the input box and press Enter.
Note
After a user has been configured, the engine ID of the GSM can be displayed by selecting Engine ID and pressing Enter.
Afterwards, test read access of the SNMP service under Linux/Unix using
snmpwalk:
$ snmpwalk -v 3 -l authPriv -u user -a sha -A password -x aes -X key 192.168.222.115
iso .3.6.1.2.1.1.1.0 = STRING: "Greenbone Security Manager"
iso .3.6.1.2.1.1.5.0 = STRING: "gsm"
...
The following information can be gathered:
- Uptime
- Network interfaces
- Memory
- Harddisk
- Load
- CPU
7.2.3.5. Configuring a Port for the Temporary HTTP Server¶
By default, the port for HTTP uploads and downloads is randomly selected.
A permanent port can be configured as follows:
Select Setup and press Enter.
Select Services and press Enter.
Select Temporary HTTP and press Enter.
Select Port and press Enter.
Enter the port in the input box and press Enter.
→ A message informs that the changes have to be saved (see Chapter 7.1.3).
Press Enter to close the message.
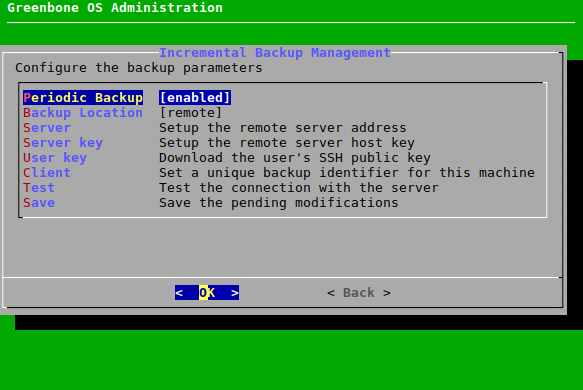
7.2.4. Configuring Periodic Backups¶
The GSM supports automatic daily backups. These backups are stored locally or remote using the following scheme:
- Last 7 daily backups
- Last 5 weekly backups
- Last 12 monthly backups
Backups older than one year will be deleted automatically. In factory state backups are disabled.
Periodic Backups can be enabled as follows:
Select Setup and press Enter.
Select Backup and press Enter.
Select Periodic Backup and press Enter (see Fig. 7.32).
→ Periodic backups are enabled.
By default, backups are stored locally. To store them on a remote server the server has to be set up appropriately. The GSM uses the Secure File Transfer Protocol (SFTP) supported by SSH to transfer the backups.
Set up a remote server as follows:
Select Setup and press Enter.
Select Backup and press Enter.
Select Backup Location and press Enter.
→ More options for the backup location are added (see Fig. 7.33).
Select Server and press Enter.
Enter the remote server address in the following format:
username@hostname[:port]/directoryNote
The optional port may be omitted if the server uses port 22.
Select OK and press Enter.
→ A message informs that the changes have to be saved (see Chapter 7.1.3).
Press Enter to close the message.
Note
The GSM uses a public key to identify the remote server before logging in.
Select Server key and press Enter.
Open the web browser and enter the displayed URL (see Fig. 7.34).
Click Browse…, select the SSH host public key and click Upload.
Tip
The SSH host public key has to be looked up on the remote backup server. On Linux and most Unix-like systems it can be found under
/etc/ssh/ssh_host_*_key.pub.Note
The GSM uses an SSH private key to log in on the remote server. To enable this login process the public key of the GSM must be enabled in the
authorized_keysfile on the remote server. The GSM generates such a private/public key pair.To download the public key select User key and press Enter.
Open the web browser and enter the displayed URL.
Download the PUB file.
Note
If several GSM appliances upload their backups to the same remote server, the files must be distinguishable. For this a unique backup identifier has to be defined. If this identifier is not set, the hostname will be used. If the hostname was modified from the default and is unique, the backup files will be distinguishable as well.
Select Client and press Enter.
Enter the identifier and press Enter.
Note
Since the setup of the remote backup including the keys is error-prone, a test routine is available. This option will test the successful login to the remote system.
Select Test and press Enter.
→ The login to the remote system is tested.
7.2.5. Configuring the Feed Synchronization¶
The Greenbone Security Feed (GSF) provides updates to the Network Vulnerability Tests (NVT), the SCAP data (CVE and CPE) and the advisories from the CERT-Bund and DFN-CERT. Additionally, the GSF provides updates for GOS.
A GSF subscription key is required to use the GSF (see Chapter 7.1.1). This key allows the GSM to download the GSF provided by Greenbone Networks.
If no valid GSF subscription key is stored on the appliance, the appliance only uses the public Greenbone Community Feed (GCF) and not the GSF.
7.2.5.1. Adding a Greenbone Security Feed (GSF) Subscription Key¶
A new GSF subscription key can be stored on the appliance by either uploading it using HTTP or by copying and pasting it using an editor.
For information about the GSF subscription key see Chapter 7.1.1.
Note
The new key will overwrite any key already stored on the appliance.
The key can be added using HTTP as follows:
Select Setup and press Enter.
Select Feed and press Enter.
Select Key(HTTP) and press Enter.
→ A message informs that the current subscription key will be overwritten (see Fig. 7.35).
Select Yes and press Enter.
Open the web browser and enter the displayed URL.
Click Browse…, select the subscription key and click Upload.
The key can be added using the editor as follows:
Select Setup and press Enter.
Select Feed and press Enter.
Select Key(Editor) and press Enter.
→ A message informs that the current subscription key will be overwritten (see Fig. 7.35).
Select Yes and press Enter.
→ The editor is opened.
Enter the subscription key.
Press Ctrl + X.
Press Y to save the changes.
Press Enter.
7.2.5.2. Enabling or Disabling Synchronization¶
The automatic synchronization of the GSF can be disabled if the GSM does not have any internet access and should not try to access the Greenbone Networks services on the internet. The synchronization can be enabled again.
The synchronization can be enabled or disabled as follows:
Select Setup and press Enter.
Select Feed and press Enter.
Select Synchronisation and press Enter.
→ The synchronization is enabled.
The synchronization can be disabled by selecting Synchronisation and pressing Enter again.
Note
The time of the automatic feed synchronization can be set by changing the maintenance time (see Chapter 7.2.11).
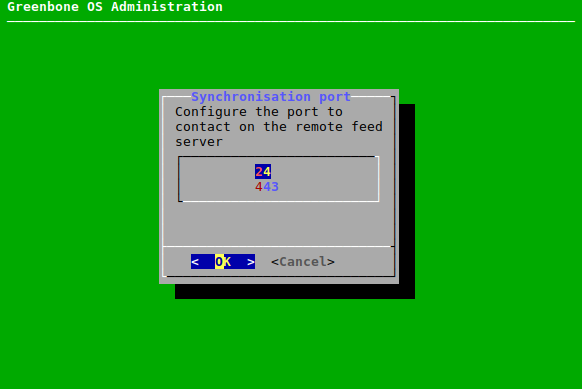
7.2.5.3. Configuring the Synchronization Port¶
The GSF is provided by Greenbone Networks on two different ports:
- 24/tcp
- 443/tcp
While port 24/tcp is the default port, many firewall setups do not allow traffic to pass to this port on the internet. So the modification of the port to 443/tcp is possible. This port is most often allowed.
The port can be configured as follows:
Select Setup and press Enter.
Select Feed and press Enter.
Select Greenbone Server and press Enter.
Select Sync port and press Enter.
Select the desired port and press Enter (see Fig. 7.36).
Note
The port 443/tcp is usually used by HTTPS traffic. While the GSM uses this port, the actual traffic is not HTTPS but SSH. The GSM uses rsync embedded in SSH to retrieve the feed. Firewalls supporting deep inspection and application awareness may still reject the traffic if these features are enabled.
7.2.5.4. Setting the Synchronization Proxy¶
If the security policy does not allow for direct internet access, the GSM can use an HTTPS proxy service. This proxy must not inspect the SSL/TLS traffic but must support the CONNECT method. The traffic passing through the proxy is not HTTPS but SSH encapsulated in http-proxy.
The proxy can be set as follows:
Select Setup and press Enter.
Select Feed and press Enter.
Select Greenbone Server and press Enter.
Select Sync proxy and press Enter.
Enter the URL of the proxy in the input box (see Fig. 7.37).
Note
The URL must have the form
http://proxy:port.
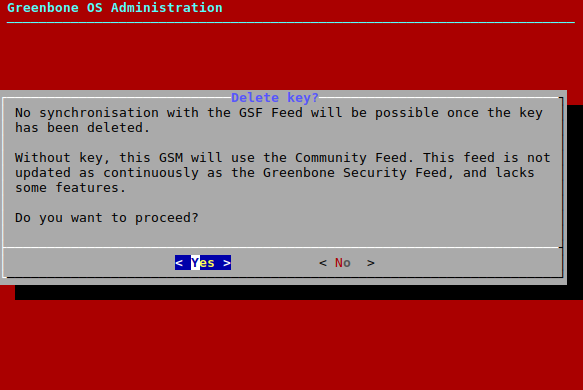
7.2.5.5. Deleting the Greenbone Security Feed (GSF) Subscription Key¶
The GSF subscription key can be removed. This is useful if an appliance is at the end of life and is not used anymore. The cleanup ensures that no licenses are left on the appliance. Without the GSF subscription key the GSM will only retrieve the Greenbone Community Feed.
There is a warning when choosing this option.
The cleanup can be done as follows:
Select Setup and press Enter.
Select Feed and press Enter.
Select Cleanup and press Enter.
→ A warning informs that the synchronization with the GSF is no longer possible after the cleanup (see Fig. 7.38).
Select Yes and press Enter.
→ A message informs that the GSF subscription key has been deleted.
Press Enter to close the message.
7.2.6. Configuring the GSM as an Airgap Master/Sensor¶
The Airgap function allows a GSM that is not directly connected to the internet to obtain feed updates and GOS upgrades.
Two GSMs are required:
- Airgap sensor: situated in a secured area and is not connected to the internet
- Airgap master: is connected to the internet
All GSM types from GSM 400 or higher can be configured as an Airgap master/sensor.
Two options are available for the Airgap function:
- Greenbone Airgap USB stick
- Airgap FTP server
7.2.6.1. Using the Airgap USB Stick¶
The updates and upgrades are loaded from a GSM that is connected to the internet and copied to a USB stick. The USB stick can then can be used to update the second GSM.
Note
The USB stick has to be a specific Greenbone Airgap USB stick provided by Greenbone Networks. Contact the Greenbone Networks support via e-mail (support@greenbone.net) providing the customer number to request a respective Airgap USB stick.
Tip
The USB stick can be checked for malware by a security gateway beforehand.
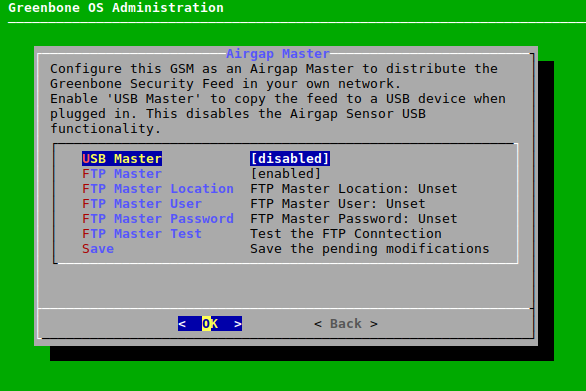
The data transfer using the Airgap USB stick is performed as follows:
In the GOS administration menu of the Airgap master select Setup and press Enter.
Select Feed and press Enter.
Select Airgap Master and press Enter.
Select USB Master and press Enter (see Fig. 7.39).
Select Save and press Enter.
Note
Configuring a GSM as an Airgap USB master disables the possibility to configure the GSM as an Airgap USB sensor.
Connect the Airgap USB stick to the Airgap master.
→ The data transfer starts automatically.
When the data transfer is finished, connect the Airgap USB stick to the Airgap sensor.
→ The data transfer starts automatically.
7.2.6.2. Using the Airgap FTP Server¶
The updates and upgrades can be provided via an FTP server operating as a data diode. A data diode is a unidirectional security gateway allowing the data flow in only one direction.
The FTP server takes on the function of the Airgap USB stick (see Chapter 7.2.6.1).
- The Airgap master picks up the updates/upgrades from the Greenbone server and writes it to the FTP server at its maintenance time.
- The Airgap sensor downloads the updates/upgrades from the FTP server at its maintenance time.
Note
Ensure that the maintenance time of the Airgap sensor is at least three hours behind the maintenance time of the Airgap master (see Chapter 7.2.7).
The data transfer using the Airgap FTP server is performed as follows:
In the GOS administration menu of the Airgap master select Setup and press Enter.
Select Feed and press Enter.
Select Airgap Master and press Enter.
Select FTP Master and press Enter.
→ Additional menu options for the configuration of the FTP server are shown (see Fig. 7.40).
Select FTP Master Location and press Enter.
Enter the path of the FTP server in the input box and press Enter.
Select FTP Master User and press Enter.
Enter the user used for logging into the FTP server in the input box and press Enter.
Select FTP Master Password and press Enter.
Enter the password used for logging into the FTP server in the input box and press Enter.
Select FTP Master Test and press Enter.
→ It is tested whether a login with the entered information is working.
Select Save and press Enter.
In the GOS administration menu of the Airgap sensor select Setup and press Enter.
Select Feed and press Enter.
Select Airgap Sensor and press Enter.
Execute steps 5 to 12 in the GOS administration menu of the Airgap sensor using the same input as for the Airgap master.
Note
The menu options have slightly different names compared to the GOS administration menu of the Airgap master (see Fig. 7.41).
→ The data transfer starts automatically.
7.2.7. Configuring the Time Synchronization¶
To synchronize the appliance with central time servers, the GSM supports the Network Time Protocol (NTP). Up to four different NTP servers can be configured. The appliance will choose the most suitable server. During an outage of one server, another server will be used automatically.
Both IP addresses and DNS names are supported.
The NTP settings can be configured as follows:
Select Setup and press Enter.
Select Timesync and press Enter.
Select Time synchronisation and press Enter.
→ The time synchronization is enabled.
Select the desired time server and press Enter (see Fig. 7.42).
Enter the time server in the input box and press Enter.
→ A message informs that the changes have to be saved (see Chapter 7.1.3).
Press Enter to close the message.
7.2.8. Selecting the Keyboard Layout¶
The keyboard layout of the appliance can be modified as follows:
Select Setup and press Enter.
Select Keyboard and press Enter.
→ All available keyboard layouts are displayed. The current layout has the annotation (selected) (see Fig. 7.43).
Select the desired keyboard layout and press Enter.
→ A message asks to confirm the change.
Select Yes and press Enter.
→ A message informs that the layout has been changed.
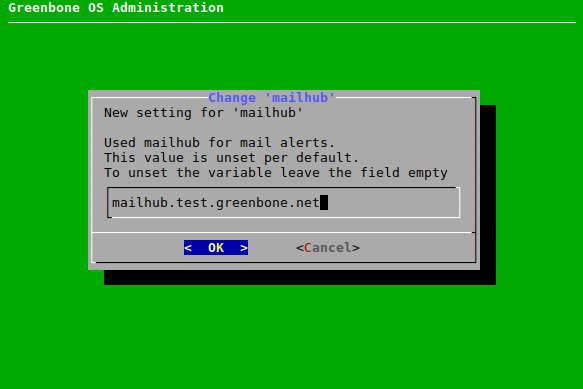
7.2.9. Configuring Automatic E-Mails¶
If reports should automatically be sent via e-mail after the completion of a scan, the appliance needs to be configured with a mail server. This server is called a mailhub or smart host. The appliance itself does not come with a mail server.
Note
The appliance does not store e-mails in case of delivery failure. There will be no second delivery attempt.
Possible spam protection on the mail server such as grey listing must be deactivated for the appliance.
Authentication using a user name and password is not supported by the appliance. The authentication must be done IP based.
7.2.9.1. Configuring the Mail Server¶
Note
Make sure that the mail server is set up correctly and securely to prevent a misuse for spam purposes.
The mail server can be configured as follows:
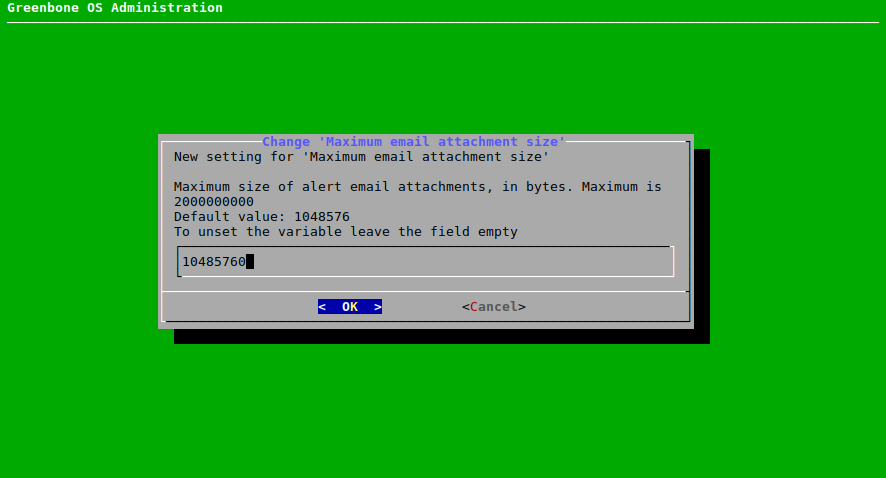
7.2.9.2. Configuring the Size of Included or Attached Reports¶
The maximum size (in bytes) of reports included in or attached to an e-mail (see Chapter 10.12) can be limited as follows:
Select Setup and press Enter.
Select Mail and press Enter.
Select Max attachment or Max include and press Enter.
Enter the maximum size (in bytes) in the input box (see Fig. 7.45).
Select OK and press Enter.
→ A message informs that the changes have to be saved (see Chapter 7.1.3).
Press Enter to close the message.
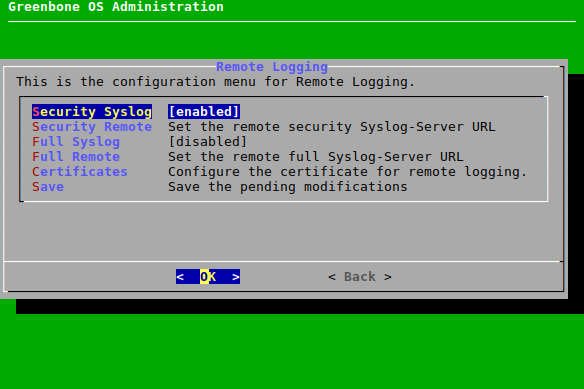
7.2.10. Configuring the Collection of Logs¶
The GSM supports the configuration of a central logging server for the collection of logs. Either only the security relevant logs or all system logs can be sent to a remote logging server. The security relevant logs contain:
- User authentication
- User authorization
The GSM uses the syslog protocol. Central collection of the logs allows for central analysis, management and monitoring of logs. Additionally, the logs are always stored locally as well.
One logging server can be configured for each kind of log (security relevant logs or all system logs).
As transport layer UDP (default), TLS and TCP can be used. TCP ensures the delivery of the logs even if a packet loss occurs. If a packet loss occurs during a transmission via UDP, the logs will be lost. TLS enables an optional authentication of the sender via TLS. This process is not RFC 5425 compliant.
7.2.10.1. Configuring the Logging Server¶
The logging server can be set up as follows:
Select Setup and press Enter.
Select Remote Syslog and press Enter.
Select Security Syslog and press Enter to enable security relevant logs (see Fig. 7.46).
or
Select Full Syslog and press Enter to enable all system logs (see Fig. 7.46).
Note
Both logs can be enabled.
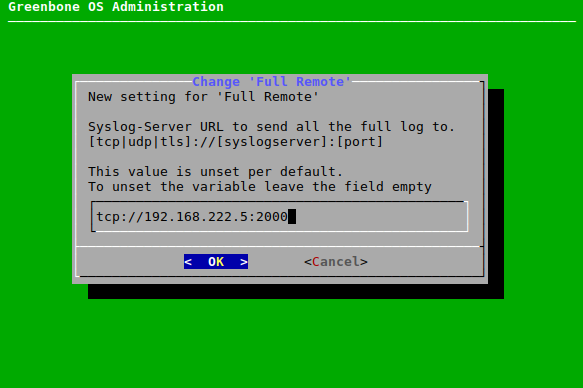
Select Security Remote and press Enter to set the logging server URL for security relevant logs.
or
Select Full Remote and press Enter to set the logging server URL for all system logs.
Enter the logging server URL in the input box (see Fig. 7.47).
Note
If no port is specified, the default port 514 will be used.
If the protocol is not specified, UDP will be used.
→ A message informs that the changes have to be saved (see Chapter 7.1.3).
Press Enter to close the message.
7.2.10.2. Managing HTTPS Certificates for Logging¶
HTTPS certificates for logging can be managed as follows:
Select Setup and press Enter.
Select Remote Syslog and press Enter.
Select Certificates and press Enter.
Select Generate and press Enter to generate a certificate.
→ A message informs that the current certificate and private key will be overwritten.
Confirm the message by selecting Yes and pressing Enter.
Enter the settings for the certificate in the input boxes (see Fig. 7.48).
Press Tab and press Enter.
→ When the process is finished, a message informs that the certificate can be downloaded.
Press Enter to close the message.
Select Certificates and press Enter.
Select Download and press Enter.
Open the web browser and enter the displayed URL.
Download the file.
In the GOS administration menu press Enter.
→ When the certificate is retrieved by the GSM, the GOS administration menu displays the fingerprint of the certificate for verification.
Check the fingerprint and confirm the certificate by pressing Enter.
→ To enable the new certificate a Reboot of the GSM is required (see Chapter 7.3.8.1).
The certificate and the according fingerprint can be displayed as follows:
Select Setup and press Enter.
Select Remote Syslog and press Enter.
Select Certificates and press Enter.
Select Show and press Enter to display the certificate.
Select Fingerprints and press Enter to display the fingerprint.
→ The following fingerprints of the currently active certificate are shown:
- SHA1
- SHA256
7.2.11. Setting the Maintenance Time¶
During maintenance the daily feed synchronization takes place. Any time during the day can be chosen except for 10:00 a.m. to 1:00 p.m. UTC. During this period Greenbone Networks itself updates the feed and disables the synchronization services.
The default maintenance time is a random time between 3:00 a.m. and 5:00 a.m. UTC.
The maintenance time can be set as follows:
Select Setup and press Enter.
Select Time and press Enter.
Enter the desired maintenance time in the input box and press Enter (see Fig. 7.49).
Note
The time has to be converted to UTC before entering it.
→ A message informs that the changes have to be saved (see Chapter 7.1.3).
Press Enter to close the message.
7.3. Maintenance Menu¶
7.3.1. Performing a Selfcheck¶
The selfcheck option checks the setup of the appliance. It displays wrong or missing configuration details which might prevent the correct function of the appliance. The following items are checked:
- Network connection
- DNS resolution
- Feed reachability
- Available updates
- User configuration
The selfcheck is performed as follows:
Select Maintenance and press Enter.
Select Selfcheck and press Enter.
→ The selfcheck is performed and any found problems are listed on the result page (see Fig. 7.50).
7.3.2. Performing and Restoring a Backup¶
Scheduled local and remote backups are configured in the menu Setup (see Chapter 7.2.4). Backups can also be performed manually. Depending on the backup location configured within Chapter 7.2.4, the manually triggered backups are stored remotely or locally. These backups can be transferred to a USB stick for offsite storage.
The backup includes all user data (e.g., tasks, reports, results) and the settings of the GSM.
7.3.2.1. Performing a Backup Manually¶
A backup can be performed manually as follows:
Select Maintenance and press Enter.
Select Backup and press Enter.
Select Incremental Backup and press Enter (see Fig. 7.51).
→ A message informs that the backup was started in the background.
Tip
The currently running system operation can be displayed by selecting About and pressing Enter in the GOS administration menu.
7.3.2.2. Restoring a Backup Manually¶
Note
Only backups created with the currently used GOS version or the previous GOS version can be restored. For GOS 6, only backups from GOS 5 or GOS 6 can be imported. If an older backup should be imported, e.g., from GOS 3 or GOS 4, an appliance with a matching GOS version has to be used.
Backups from GOS versions newer than the currently used GOS version are not supported as well. If a newer backup should be imported, an appliance with a matching GOS version has to be used.
Additionally, only backups created with the same GSM class (see Chapter 3) can be restored.
If there are any questions, contact the Greenbone Networks Support via e-mail (support@greenbone.net).
A backup can be restored as follows:
Select Maintenance and press Enter.
Select Backup and press Enter.
Select List and press Enter
Select the desired backup and press Enter.
Select Yes and press Enter if the system settings should be restored as well.
or
Select No and press Enter if only the data should be restored.
Note
The system settings include all GOS configurations, e.g., the network settings. The data includes all vulnerability scanning and vulnerability management information.
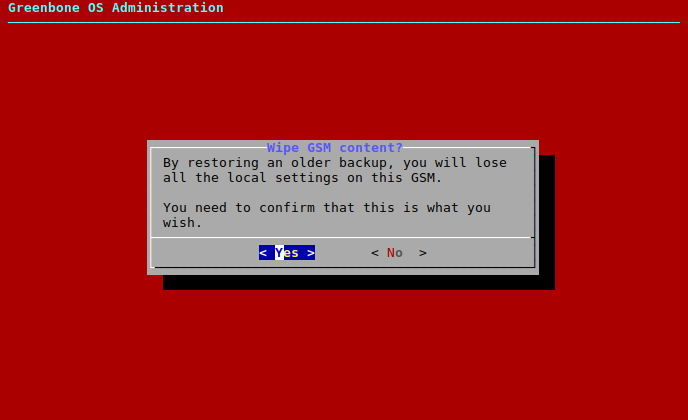
→ A warning informs that all local settings are lost if the backup is restored (see Fig. 7.52).
Confirm the message by selecting Yes and pressing Enter.
→ A message informs that the restoration was started in the background.
Tip
The currently running system operation can be displayed by selecting About and pressing Enter in the GOS administration menu.
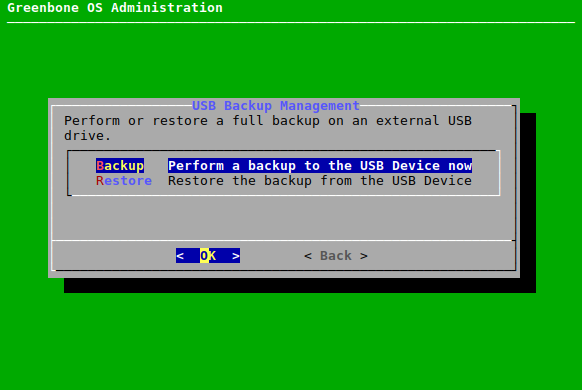
7.3.2.3. Performing a Backup Using a USB Stick¶
Backups can be transferred to a USB stick as follows:
Connect a USB stick to the GSM.
Note
A FAT-formatted USB stick has to be used. In case of problems, another USB stick or another USB port on the GSM should be tried.
Select Maintenance and press Enter.
Select Backup and press Enter.
Select USB Backup and press Enter.
Select Backup and press Enter (see Fig. 7.53).
→ A message asks to confirm the backup.
Select Yes and press Enter.
→ A message informs that the backup was started in the background.
Tip
The currently running system operation can be displayed by selecting About and pressing Enter in the GOS administration menu.
7.3.2.4. Restoring a Backup Using a USB Stick¶
Note
Only backups created with the currently used GOS version or the previous GOS version can be restored. For GOS 6, only backups from GOS 5 or GOS 6 can be imported. If an older backup should be imported, e.g., from GOS 3 or GOS 4, an appliance with a matching GOS version has to be used.
Backups from GOS versions newer than the currently used GOS version are not supported as well. If a newer backup should be imported, an appliance with a matching GOS version has to be used.
Additionally, only backups created with the same GSM class (see Chapter 3) can be restored.
If there are any questions, contact the Greenbone Networks Support via e-mail (support@greenbone.net).
Backups can be restored from a USB stick as follows:
Connect a USB stick to the GSM.
Note
A FAT-formatted USB stick has to be used. In case of problems, another USB stick or another USB port on the GSM should be tried.
Select Maintenance and press Enter.
Select Backup and press Enter.
Select USB Backup and press Enter.
Select Restore and press Enter (see Fig. 7.53).
Select Yes and press Enter if the system settings should be restored as well.
or
Select No and press Enter if only the data should be restored.
Note
The system settings include all GOS configurations, e.g., the network settings. The data includes all vulnerability scanning and vulnerability management information.
→ A warning informs that all local settings are lost if the backup is restored (see Fig. 7.54).
Confirm the message by selecting Yes and pressing Enter.
→ A message informs that the restoration was started in the background.
Tip
The currently running system operation can be displayed by selecting About and pressing Enter in the GOS administration menu.
7.3.3. Performing a GOS Upgrade¶
During the daily feed update the appliance will also download new GOS upgrades if available. While the upgrades are automatically downloaded, they are not automatically installed.
Note
Since the upgrades might interrupt current scan tasks, they need to be scheduled carefully.
Upgrades can be installed manually as follows:
Select Maintenance and press Enter.
Select Upgrade and press Enter.
Select Upgrade and press Enter to install an upgrade.
or
Select Switch Release and press Enter to switch to a new release.
→ A message informs that the upgrade was started in the background.
Tip
The currently running system operation can be displayed by selecting About and pressing Enter in the GOS administration menu.
Note
By default, a successful GOS upgrade on the master starts a GOS upgrade on connected sensors as well. Nonetheless, an upgrade can manually be installed on sensors (see Chapter 7.3.4).
7.3.4. Performing a GOS Upgrade on Sensors¶
A GOS upgrade on a sensor can be installed as follows:
Select Maintenance and press Enter.
Select Upgrade and press Enter.
Select Sensors and press Enter.
Select the desired sensor and press Space.
→ The sensor is marked with *. Multiple sensors can be selected at the same time.
Sensors that are not ready for an upgrade are labelled accordingly.
Press Enter.
→ A message informs that the upgrade was started in the background.
Tip
The currently running system operation can be displayed by selecting About and pressing Enter in the GOS administration menu.
7.3.5. Performing a Feed Update¶
By default, the appliance will try to download new feeds and GOS upgrades daily.
The feed synchronization can be triggered manually as follows:
Select Maintenance and press Enter.
Select Feed and press Enter.
Select Update and press Enter (see Fig. 7.55).
→ A message informs that the feed update was started in the background.
Tip
The currently running system operation can be displayed by selecting About and pressing Enter in the GOS administration menu.
Note
By default, a successful feed update on the master starts a feed update on connected sensors as well. Nonetheless, a feed update can manually be pushed to sensors (see Chapter 7.3.6).
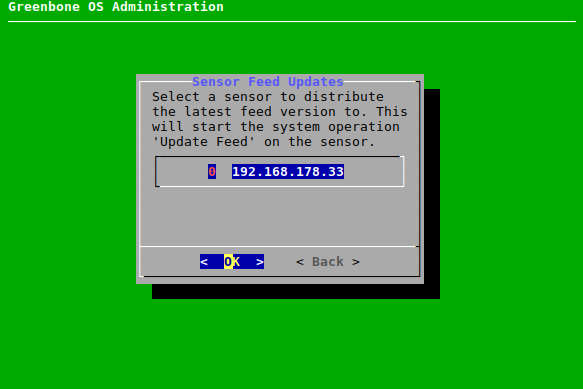
7.3.6. Performing a Feed Update on Sensors¶
A feed update can be pushed to a sensor as follows:
Select Maintenance and press Enter.
Select Feed and press Enter.
Select Sensors and press Enter.
Select the desired sensor and press Enter (see Fig. 7.56).
→ A message informs that the feed update was started in the background.
Tip
The currently running system operation can be displayed by selecting About and pressing Enter in the GOS administration menu.
7.3.7. Upgrading the Flash Partition¶
The flash partition is used to perform factory resets of the GSM. To make factory resets easier, it should be upgraded to the latest GOS version.
Note
Make sure the GSM itself is able to establish a connection to the Greenbone Feed Server.
It is not possible to upgrade the flash partition of sensors via the master.
The flash partition can be upgraded as follows:
Upgrade the GSM to the latest GOS version (see Chapter 7.3.3).
Select Maintenance and press Enter.
Select Flash and press Enter.
Select Download and press Enter (see Fig. 7.57).
→ The latest flash image is downloaded.
Tip
The currently running system operation can be displayed by selecting About and pressing Enter in the GOS administration menu.
When the download is finished, select Write and press Enter (see Fig. 7.57) .
→ The image is written to the flash partition. The process may take up to 20 minutes.
Tip
The currently running system operation can be displayed by selecting About and pressing Enter in the GOS administration menu.
7.3.8. Shutting down and Rebooting the Appliance¶
Important
The GSM should not be turned off using the power switch.
The appliance should be shut down and rebooted using the GOS administration menu instead. This ensures that mandatory cleanup processes are run during the shutdown and reboot.
7.3.8.1. Rebooting the Appliance¶
The appliance is rebooted as follows:
Select Maintenance and press Enter.
Select Power and press Enter.
Select Reboot and press Enter.
→ A message asks to confirm the reboot (see Fig. 7.58).
Select Yes and press Enter.
→ The appliance will reboot. The reboot process may take up to several minutes.
7.3.8.2. Shutting down the Appliance¶
The appliance is shut down as follows:
Select Maintenance and press Enter.
Select Power and press Enter.
Select Shutdown and press Enter.
→ A message asks to confirm the shutdown (see Fig. 7.59).
Select Yes and press Enter.
→ The appliance will shutdown. The shutdown process may take up to several minutes.
7.4. Advanced Menu¶
7.4.1. Displaying Log Files of the GSM¶
The log files of the GSM can be displayed as follows:
Select Advanced and press Enter.
Select Logs and press Enter.
Select the desired logs and press Enter (see Fig. 7.60).
→ The log file is displayed in a viewer.
Press q to quit the viewer.
7.4.2. Performing Advanced Administrative Work¶
7.4.2.1. Managing the Superuser Account¶
When the shell is accessed, a Linux command line as the unprivileged user admin is displayed (see Chapter 7.4.2.3). Any Linux command can be executed.
Note
The privileged account root (superuser) should only be used in consultation with the Greenbone Networks Support (support@greenbone.net).
If any modifications are done without consultation, the entitlement to receive assistance by the Greenbone Networks Support expires.
To obtain root privileges on the GSM, the command su has to be entered in the shell.
Using su to switch from the admin user to the root user is disabled by default.
The superuser has to be enabled and provided with a password as follows:
Select Advanced and press Enter.
Select Support and press Enter.
Select Superuser and press Enter.
Select Superuser State and press Enter (see Fig. 7.61).
→ A warning informs that root privileges should only be obtained by exception and while consulting the Greenbone Networks Support (support@greenbone.net).
Select Yes and press Enter.
→ A message informs that the changes have to be saved (see Chapter 7.1.3).
Press Enter to close the message.
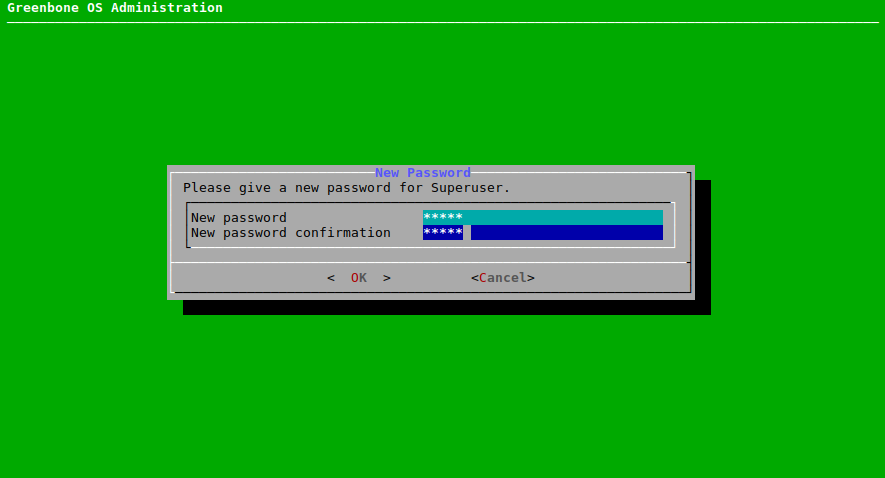
Select Password and press Enter (see Fig. 7.61).
Enter the password twice, select OK and press Enter (see Fig. 7.62).
7.4.2.2. Generating and Downloading a Support Package¶
Sometimes the Greenbone Networks Support requires additional information to troubleshoot and support customers. The required data is collected as an (encrypted) support package including all configuration data of the GSM appliance.
The package can be encrypted using the GPG public key of the Greenbone Networks Support. The support package is stored on the appliance.
A support package can be created as follows:
Select Advanced and press Enter.
Select Support and press Enter.
Select Support Package and press Enter.
→ A message asks to confirm the generation of the support package.
Select Yes and press Enter.
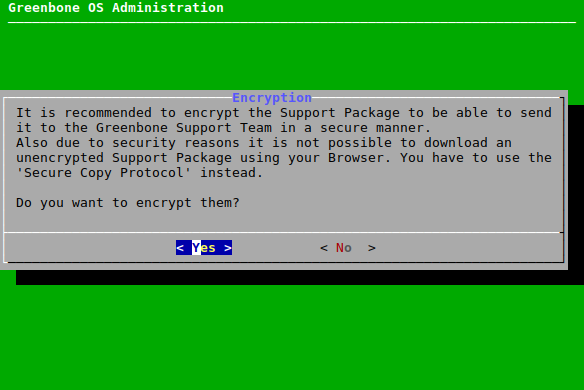
→ A message asks whether the support package should be encrypted (see Fig. 7.63).
Select Yes and press Enter to encrypt the support package.
or
Select No and press Enter to not encrypt the support package.
If an encrypted support package was chosen, open the web browser, enter the displayed URL and download the GPG file (encrypted ZIP folder).
or
Note
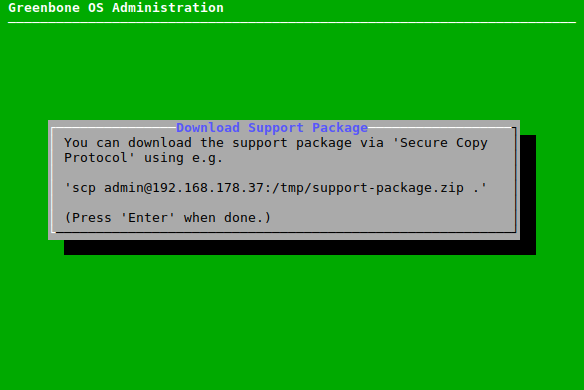
If the support package is not encrypted, the download needs to be done using the Secure Copy Protocol (SCP). For this, SSH has to be enabled first (see Chapter 7.2.3.3).
If an unencrypted support package was chosen, enter the displayed command using SCP (see Fig. 7.64) and download the support package (ZIP folder).
Note
The “.” at the end can be replaced with a path. If the “.” is maintained, the current folder is chosen.
Send the ZIP folder via e-mail to the Greenbone Networks Support (support@greenbone.net).
On Microsoft Windows systems the support package can be downloaded using either pscp, a command line tool included in PuTTY, or smarTTY, a graphical tool implementing SCP.
7.4.2.3. Accessing the Shell¶
Shell access is not required for any administrative work, but may be requested by Greenbone Networks Support for diagnostics and support.
The shell can be accessed as follows:
Select Advanced and press Enter.
Select Support and press Enter.
Select Shell and press Enter.
→ A warning informs that the shell level is undocumented and should not be used for administrative settings (see Fig. 7.65).
Select Continue and press Enter.
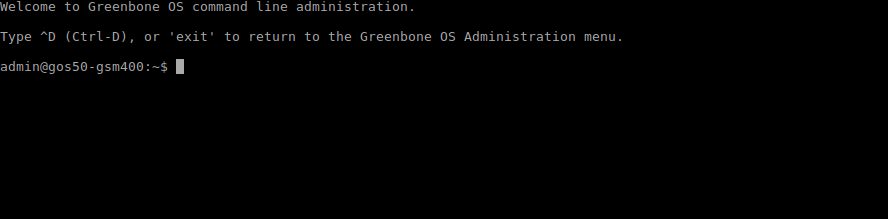
→ A Linux shell is opened using the unprivileged user admin (see Fig. 7.66).
Note
Accessing as root requires the enabling of the superuser and the determination of a password (see Chapter 7.4.2.1). Afterwards, switching to root using the command
suis possible.Enter
exitor press Ctrl + D to quit the shell.
7.4.3. Displaying the Greenbone Security Feed (GSF) Subscription Key¶
The GSF subscription key (see Chapter 7.2.5.1) can be displayed as follows:
Select Advanced and press Enter.
Select Subscription and press Enter (see Fig. 7.67).
→ The subscription key is displayed in a viewer.
Press q to quit the viewer.
7.5. Displaying Information about the Appliance¶
Information about the GSM can be displayed by selecting About and pressing Enter.
The following information is displayed:
- GSM type
- GOS version
- Feed version
- Name of the GSF subscription key
- IP address of the web interface
- Configured sensors
- Currently running system operations