13. Managing SecInfo¶
The SecInfo management provides centralized access to a wide range of information technology (IT) security information including the following categories:
- Network Vulnerability Tests (NVT)
- NVTs test the target system for potential vulnerabilities.
- Common Vulnerabilities and Exposures (CVE)
- CVEs are vulnerabilities published by vendors and security researchers.
- Common Platform Enumeration (CPE)
- CPE offers standardized names for products used in the IT.
- Open Vulnerability Assessment Language (OVAL) Definitions
- OVAL offers a standardized language for testing vulnerabilities. OVAL definitions use this language to discover vulnerabilities.
- CERT-Bund Advisories
- CERT-Bund Advisories are published by the Emergency Response Team of the Federal Office for Information Security (German: Bundesamt für Sicherheit in der Informationstechnik, abbreviated as BSI). The main task of the CERT-Bund is the operation of a warning and information service publishing information regarding new vulnerabilities and security risks as well as threats for IT systems.
- DFN-CERT Advisories
- The DFN-CERT is the emergency response team of the German Research Network (German: Deutsches Forschungsnetz, abbreviated as DFN).
CVEs, CPEs and OVAL definitions are published and made accessible by NIST as part of the National Vulnerability Database (NVD) (see Chapter 13.2).
Note
Greenbone Networks is also offering all SecInfo data online, accessible via the SecInfo portal. The SecInfo portal provides all SecInfo described in the following chapters and the CVSS calculator.
Access to the SecInfo Portal is provided by activating a guest access (see Chapter 9.1.3).
13.1. Network Vulnerability Tests (NVT)¶
NVTs are test routines used by the GSM. They are part of the Greenbone Security Feed (GSF) which is updated regularly. NVTs include information about development date, affected systems, impact of vulnerabilities and remediation.
List Page
All existing NVTs can be displayed by selecting SecInfo > NVTs in the menu bar.
For all NVTs the following information is displayed:
- Name
- Name of the NVT.
- Family
- Family of NVTs to which the NVT belongs.
- Created
- Date and time of creation.
- Modified
- Date and time of last modification.
- CVE
- CVE that is checked for using the NVT.
- Solution Type

Solution for the vulnerability. The following solutions are possible:
- Severity
- The severity of the vulnerability (CVSS, see Chapter 13.2.4) is displayed as a bar to support the analysis of the results.
- QoD
QoD is short for Quality of Detection and represents how reliable the detection of a vulnerability is. The QoD concept was introduced with GOS 3.1. Results created with GOS versions before GOS 3.1 were assigned a QoD of 75 % during migration.
With the introduction of the QoD, the parameter Paranoid in the scan configuration (see Chapter 10.9) is removed without replacement. In the past a scan configuration without this parameter only used NVTs with a QoD of at least 70%. Now all NVTs are used and executed in a scan configuration.
Note
By clicking  below the list of NVTs more than one NVT can be exported at a time. The drop-down-list is used to select which NVTs are exported.
below the list of NVTs more than one NVT can be exported at a time. The drop-down-list is used to select which NVTs are exported.
Details Page
Click on the name of an NVT to display the details of the NVT. Click  to open the details page of the NVT.
to open the details page of the NVT.
The following actions are available in the upper left corner:
13.2. Security Content Automation Protocol (SCAP)¶
The National Institute of Standards and Technology (NIST) provides the National Vulnerability Database (NVD). NVD is a data repository for the vulnerability management of the US government. The goal is the standardized provision of the data for automated processing. By that, vulnerability management is supported and the implementation of compliance guidelines is verified.
The NVD provides different databases including the following:
- Checklists
- Vulnerabilities
- Misconfigurations
- Products
- Threat metrics
The NVD utilizes the Security Content Automation Protocol (SCAP). SCAP is a combination of different interoperable standards. Many standards were developed or derived from public discussion.
The public participation of the community in the development is an important aspect for accepting and spreading SCAP standards. SCAP is currently specified in version 1.2 and includes the following components:
- Languages
- XCCDF: Extensible Configuration Checklist Description Format
- OVAL: Open Vulnerability and Assessment Language
- OCIL: Open Checklist Interactive Language
- Asset Identification
- ARF: Asset Reporting Format
- Collections
- CCE: Common Configuration Enumeration
- CPE: Common Platform Enumeration
- CVE: Common Vulnerabilities and Exposure
- Metrics
- CVSS: Common Vulnerability Scoring System
- CCSS: Common Configuration Scoring System
- Integrity
- TMSAD: Trust Model for Security Automation Data
OVAL, CCE, CPE and CVE are trademarks of NIST.
The Greenbone Security Manager (GSM) uses OVAL, CVE, CPE and CVSS. By utilizing these standards the interoperability with other systems is guaranteed. The standards also allow comparing the results.
Vulnerability assessment systems such as the GSM can be validated by NIST respectively. The GSM has been validated with respect to SCAP version 1.0.
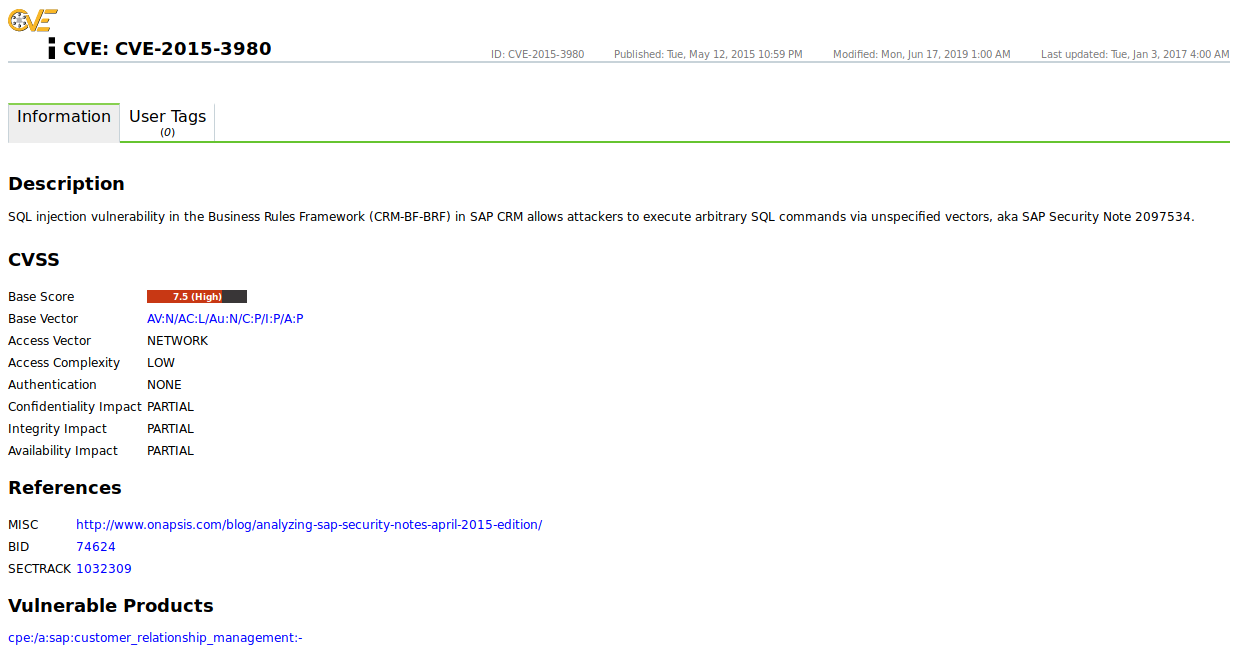
13.2.1. CVE¶
In the past, various organizations discovered and reported vulnerabilities at the same time and assigned them different names. This led to different scanners reporting the same vulnerability under different names making communication and comparison of the results complicated.
To address this, MITRE founded the Common Vulnerabilities and Exposure (CVE) project. Every vulnerability is assigned a unique identifier consisting of the release year and a simple number. This identifier serves as a central reference.
The CVE database of MITRE is not a vulnerability database. CVE was developed in order to connect the vulnerability database and other systems with each other enabling the comparison of security tools and services.
The CVE database does not contain detailed technical information or any information regarding risk, impact or elimination of the vulnerability. A CVE only contains the identification number with the status, a short description and references to reports and advisories.
The NVD refers to the CVE database and complements the content with information regarding the elimination, severity, possible impact and affected products of the vulnerability. Greenbone Networks refers to the CVE database of the NVD. At the same time the GSM combines the information, NVTs and CERT-Bund/DFN-CERT advisories.
List Page
All existing CVEs can be displayed by selecting SecInfo > CVEs in the menu bar.
The column Severity may display N/A for one of the following reasons:
The CVE was published but no vulnerability analysis/severity assessment was carried out by the NVD yet. This can take a few days up to a few weeks.
Such CVEs can be identified when browsing the related entry. As long as Undergoing Analysis is displayed there, N/A is shown in the column Severity for the CVE.
There is always a delay of 1 – 2 working days between the vulnerability analysis/severity assessment and the time the severity is displayed in the SecInfo.
Note
By clicking  below the list of CVEs more than one CVE can be exported at a time. The drop-down-list is used to select which CVEs are exported.
below the list of CVEs more than one CVE can be exported at a time. The drop-down-list is used to select which CVEs are exported.
Details Page
Click on the name of a CVE to display the details of the CVE. Click  to open the details page of the CVE (see Fig. 13.1).
to open the details page of the CVE (see Fig. 13.1).
The following registers are available:
- Information
- General information about the CVE.
- User Tags
- Assigned tags (see Chapter 8.5).
The following actions are available in the upper left corner:
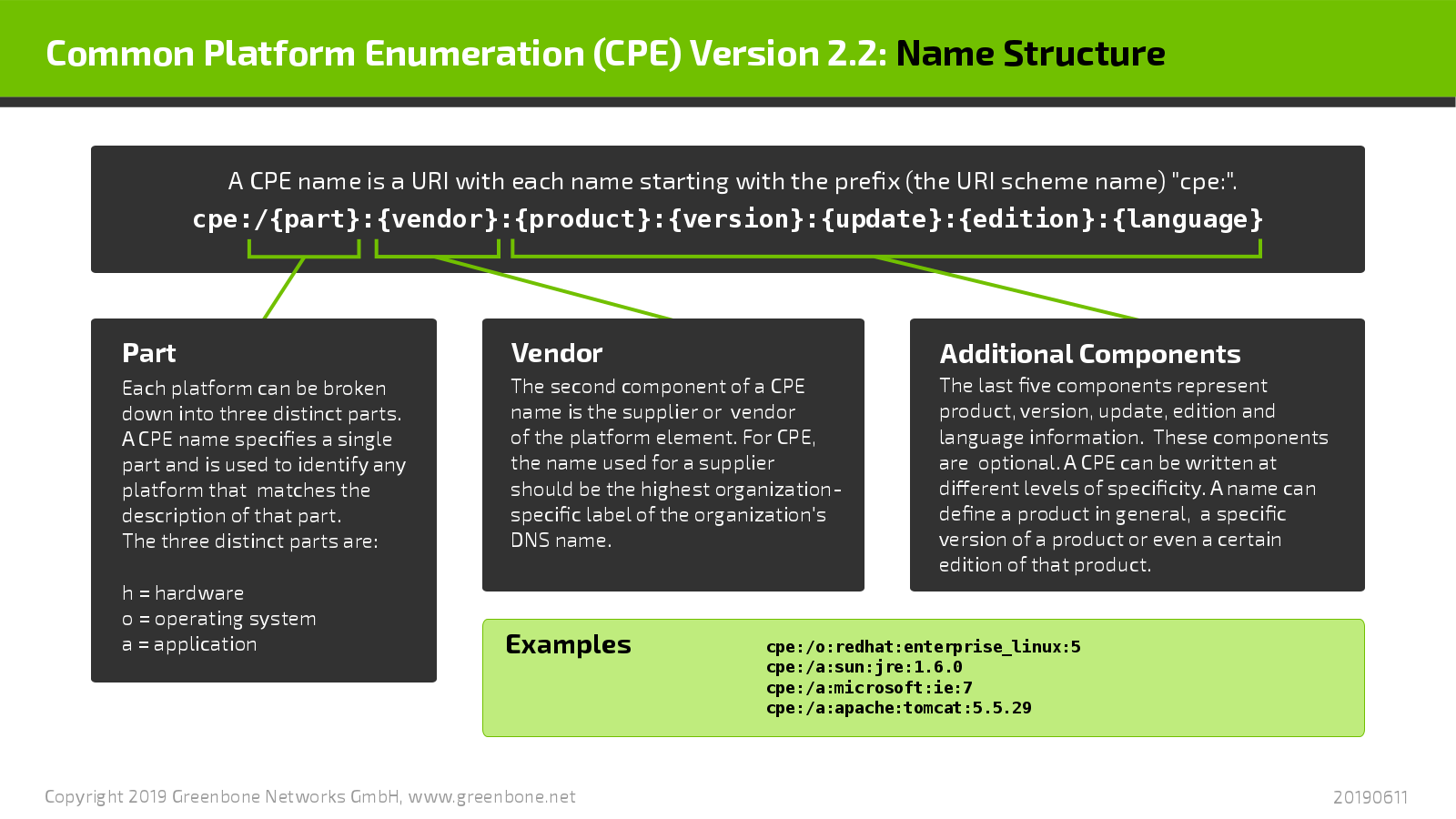
13.2.2. CPE¶
The Common Platform Enumeration (CPE) is modelled after CVE. It is a structured naming scheme for applications, operating systems and hardware devices.
The CPE was initiated by MITRE and is maintained by NIST as a part of the NVD. NIST has already maintained the official CPE dictionary and the CPE specifications for many years. CPE is based on the generic syntax of the Uniform Resource Identifier (URI).
The combination of CPE and CVE standards enables the conclusion of existing vulnerabilities when discovering a platform or product.
CPE is composed of the following components:
- Naming
- The name specification describes the logical structure of well-formed names (WFNs), their binding to URIs and formatted character strings as well as their conversion.
- Name Matching
- The name matching specification describes the methods to compare WFNs with each other. This allows for the testing whether some or all WFNs refer to the same product.
- Dictionary
- The dictionary is a repository of CPE names and metadata. Every name defines a single class of an IT product. The dictionary specification describes the processes for using the dictionary, e.g. searching for a specific name or for entries belonging to a more general class.
- Applicability Language
- The applicability language specification describes the creation of complex logical expressions with the help of WFNs. These applicability statements can be used for tagging checklists, guidelines or other documents and, by that, for describing for which products the documents are relevant.
List Page
All existing CPEs can be displayed by selecting SecInfo > CPEs in the menu bar.
Note
By clicking  below the list of CPEs more than one CPE can be exported at a time. The drop-down-list is used to select which CPEs are exported.
below the list of CPEs more than one CPE can be exported at a time. The drop-down-list is used to select which CPEs are exported.
Details Page
Click on the name of a CPE to display the details of the CPE. Click  to open the details page of the CPE.
to open the details page of the CPE.
The following registers are available:
- Information
- General information about the CPE.
- User Tags
- Assigned tags (see Chapter 8.5).
The following actions are available in the upper left corner:
13.2.3. OVAL Definitions¶
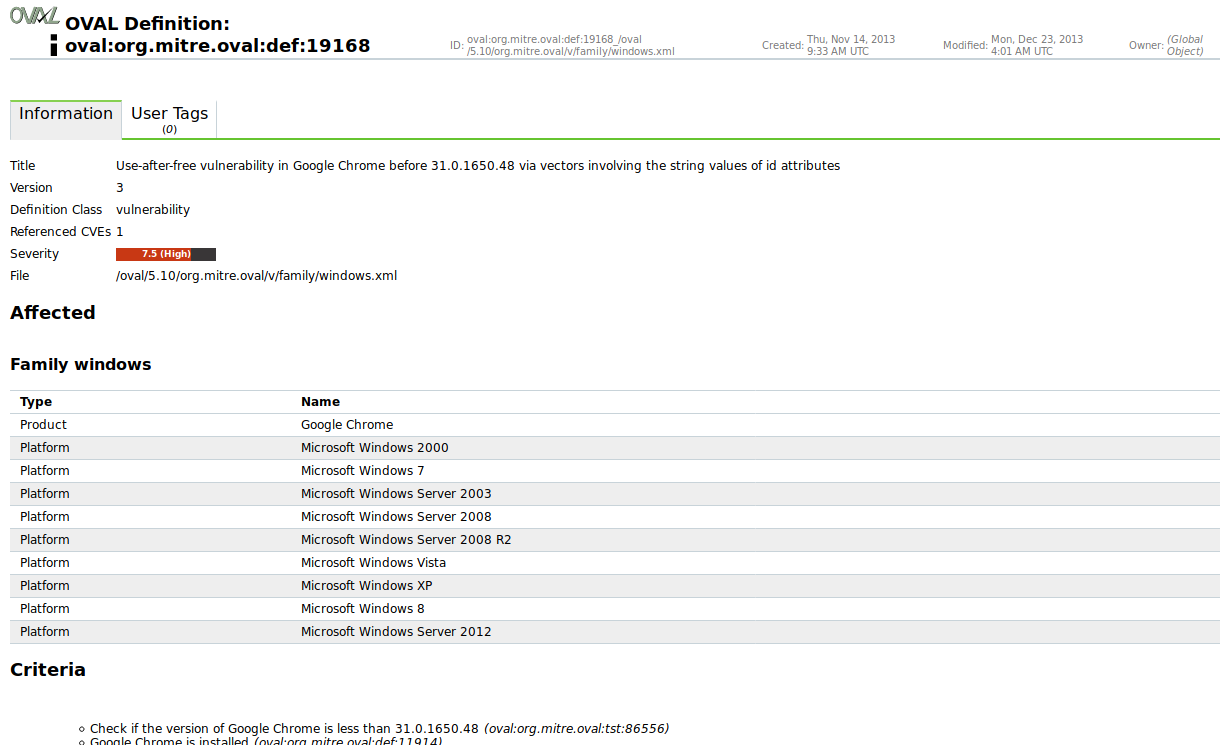
The Open Vulnerability and Assessment Language (OVAL) is a MITRE project.
OVAL is a language to describe vulnerabilities, configuration settings (compliance), patches and applications (inventory).
The XML based definitions allow simple processing by automated systems and describe the discovery of individual systems and vulnerabilities.
Example: the OVAL definition 22272 has the following structure:
<definition id="oval:org.mitre.oval:def:22272" version="4" class="vulnerability">
<metadata>
<title>Vulnerability in Google Chrome before 32.0.1700.76 on Windows allows
attackers to trigger a sync with an arbitrary Google account by
leveraging improper handling of the closing of an untrusted signin
confirm dialog</title>
<affected family="windows">
<platform>Microsoft Windows 2000</platform>
<platform>Microsoft Windows XP</platform>
<platform>Microsoft Windows Server 2003</platform>
<platform>Microsoft Windows Server 2008</platform>
<platform>Microsoft Windows Server 2008 R2</platform>
<platform>Microsoft Windows Vista</platform>
<platform>Microsoft Windows 7</platform>
<platform>Microsoft Windows 8</platform>
<platform>Microsoft Windows 8.1</platform>
<platform>Microsoft Windows Server 2012</platform>
<platform>Microsoft Windows Server 2012 R2</platform>
<product>Google Chrome</product>
</affected>
<reference source="CVE" ref_id="CVE-2013-6643"
ref_url="http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-6643"/>
<description>The OneClickSigninBubbleView::WindowClosing function in
browser/ui/views/sync/one_click_signin_bubble_view.cc in Google
Chrome before 32.0.1700.76 on Windows and before 32.0.1700.77 on Mac
OS X and Linux allows attackers to trigger a sync with an arbitrary
Google account by leveraging improper handling of the closing of an
untrusted signin confirm dialog.</description>
<oval_repository>
<dates>
<submitted date="2014-02-03T12:56:06">
<contributor organization="ALTX-SOFT">Maria Kedovskaya</contributor>
</submitted>
<status_change date="2014-02-04T12:25:48.757-05:00">DRAFT</status_change>
<status_change date="2014-02-24T04:03:01.652-05:00">INTERIM</status_change>
<status_change date="2014-03-17T04:00:17.615-04:00">ACCEPTED</status_change>
</dates>
<status>ACCEPTED</status>
</oval_repository>
</metadata>
<criteria>
<extend_definition comment="Google Chrome is installed"
definition_ref="oval:org.mitre.oval:def:11914"/>
<criteria operator="AND" comment="Affected versions of Google Chrome">
<criterion comment="Check if the version of Google Chrome is greater than
or equals to 32.0.1651.2" test_ref="oval:org.mitre.oval:tst:100272"/>
<criterion comment="Check if the version of Google Chrome is less than
or equals to 32.0.1700.75" test_ref="oval:org.mitre.oval:tst:99783"/>
</criteria>
</criteria>
</definition>
This information is graphically processed by the web interface and presented easily readable.
List Page
All existing OVAL definitions can be displayed by selecting SecInfo > OVAL Definitions in the menu bar.
Note
By clicking  below the list of OVAL definitions more than one OVAL definition can be exported at a time. The drop-down-list is used to select which OVAL definitions are exported.
below the list of OVAL definitions more than one OVAL definition can be exported at a time. The drop-down-list is used to select which OVAL definitions are exported.
Details Page
Click on the name of an OVAL definition to display the details of the OVAL definition. Click  to open the details page of the OVAL definition (see Fig. 13.3).
to open the details page of the OVAL definition (see Fig. 13.3).
The following registers are available:
- Information
- General information about the OVAL definition.
- User Tags
- Assigned tags (see Chapter 8.5).
The following actions are available in the upper left corner:
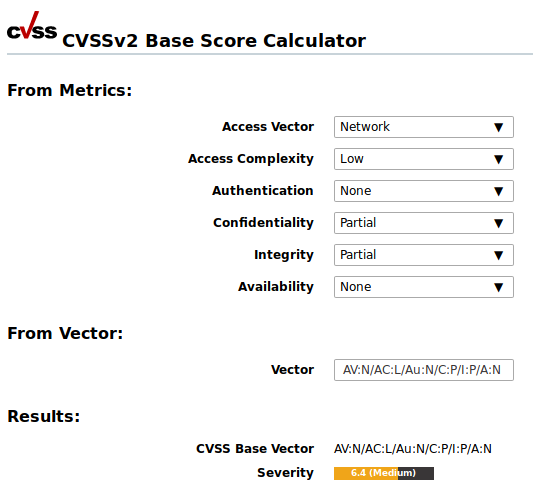
13.2.4. CVSS¶
To support the interpretation of a vulnerability, the Common Vulnerability Scoring System (CVSS) was invented. The CVSS is an industry standard for describing the severity of security risks in computer systems.
Security risks are rated and compared using different criteria. This allows for the creation of a priority list of counter measures.
The CVSS is developed by the CVSS Special Interest Group (CVSS-SIG) of the Forum of Incident Response and Security Teams (FIRST). The current CVSS score version is 3.1.
Note
GOS 5.0 only supports CVSS score version 2.
The CVSS score in version 2 supports base score metrics, temporal score metrics and environmental score metrics.
- Base score metrics
- Base score metrics test the exploitability of a vulnerability and their impact on the target system. Access, complexity and requirement of authentication are rated. Additionally, they rate whether the confidentiality, integrity or availability is threatened.
- Temporal score metrics
- Temporal score metrics test whether a completed example code exists, the vendor already supplied a patch and confirmed the vulnerability. The score will be changing drastically in the course of time.
- Environmental score metrics
- Environmental score metrics describe the effect of a vulnerability within an organization. They take damage, target distribution, confidentiality, integrity and availability into account. This assessment strongly depends on the environment in which the vulnerable product is used.
Since the base score metrics are merely meaningful in general and can be determined permanently, the GSM provides them as part of the SecInfo data.
The CVSS calculator can be opened by selecting Extras > CVSS Calculator in the menu bar (see Fig. 13.4).
The following formula is used by the CVSS calculator:
BaseScore = roundTo1Decimal( ( ( 0.6 * Impact ) +
( 0.4 * Exploitability ) - 1.5 ) * f( Impact ) )
“Impact” is calculated as follows:
Impact = 10.41 * (1 - (1 - ConfImpact) *
(1 - IntegImpact) * (1 - AvailImpact))
“Exploitability” is calculated as follows:
Exploitability = 20 * AccessVector * AccessComplexity * Authentication
Note
The function f( Impact ) is 0, if the impact is 0.
In all other cases the value is 1.176.
The other values are constants:
- Access Vector
- Requires local access: 0.395
- Adjacent network accessible: 0.646
- Network accessible: 1.0
- Access Complexity
- High: 0.35
- Medium: 0.61
- Low: 0.71
- Authentication
- Requires multiple instances of authentication: 0.45
- Requires single instance of authentication: 0.56
- Requires no authentication: 0.704
- ConfImpact
- None: 0.0
- Partial: 0.275
- Complete: 0.660
- IntegImpact
- None: 0.0
- Partial: 0.275
- Complete: 0.660
- AvailImpact
- None: 0.0
- Partial: 0.275
- Complete: 0.660
13.3. CERT-Bund Advisories¶
The CERT-Bund (Computer Emergency Response Team for Federal Agencies) is the central point of contact for preventive and reactive measures regarding security related computer incidents.
With the intention of avoiding harm and limiting potential damage, the work of CERT-Bund includes the following:
- Creating and publishing recommendations for preventive measures
- Pointing out vulnerabilities in hardware and software products
- Proposing measures to address known vulnerabilities
- Supporting public agencies efforts to respond to IT security incidents
- Recommending various mitigation measures
Additionally, CERT-Bund operates the German IT Situation Centre.
The services of CERT-Bund are primarily available to federal authorities and include the following:
- 24 hour on call duty in cooperation with the IT Situation Centre
- Analyzing incoming incident reports
- Creating recommendations derived from incidents
- Supporting federal authorities during IT security incidents
- Operating a warning and information service
- Active alerting of the federal administration in case of imminent danger
The CERT-Bund offers a warning and information service (German: Warn- und Informationsdienst, abbreviated as “WID”). Currently this service offers two different types of information:
- Advisories
- This information service is only available to federal agencies as a closed list. The advisories describe current information about security critical incidents in computer systems and detailed measures to remediate security risks.
- Short Information
- Short information features the short description of current information regarding security risks and vulnerabilities. This information is not always verified and could be incomplete or even inaccurate.
The Greenbone Security Feed contains the CERT-Bund Short Information.
They can be identified by the “K” in the message (CB-K14/1296).
List Page
All existing CERT-Bund advisories can be displayed by selecting SecInfo > CERT-Bund Advisories in the menu bar.
Note
By clicking  below the list of CERT-Bund advisories more than one CERT-Bund advisory can be exported at a time. The drop-down-list is used to select which CERT-Bund advisories are exported.
below the list of CERT-Bund advisories more than one CERT-Bund advisory can be exported at a time. The drop-down-list is used to select which CERT-Bund advisories are exported.
Details Page
Click on the name of a CERT-Bund advisory to display the details of the CERT-Bund advisory. Click  to open the details page of the CERT-Bund advisory.
to open the details page of the CERT-Bund advisory.
The following registers are available:
- Information
- General information about the CERT-Bund advisory.
- User Tags
- Assigned tags (see Chapter 8.5).
The following actions are available in the upper left corner:
13.4. DFN-CERT Advisories¶
While the individual NVTs, CVEs, CPEs and OVAL definitions are created primarily to be processed by computer systems, the DFN-CERT publishes new advisories regularly.
The DFN-CERT is responsible for hundreds of universities and research institutions that are associated with the German Research Network (German: Deutsches Forschungsnetz, abbreviated as DFN). Additionally, it provides key security services to government and industry.
An advisory describes especially critical security risks that require fast reacting. The DFN-CERT advisory service includes the categorization, distribution and rating of advisories issued by different software vendors and distributors. Advisories are obtained by the Greenbone Security Manager and stored in the database for reference.
List Page
All existing DFN-CERT advisories can be displayed by selecting SecInfo > DFN-CERT Advisories in the menu bar.
Note
By clicking  below the list of DFN-CERT advisories more than one DFN-CERT advisory can be exported at a time. The drop-down-list is used to select which DFN-CERT advisories are exported.
below the list of DFN-CERT advisories more than one DFN-CERT advisory can be exported at a time. The drop-down-list is used to select which DFN-CERT advisories are exported.
Details Page
Click on the name of a DFN-CERT advisory to display the details of the DFN-CERT advisory. Click  to open the details page of the DFN-CERT advisory.
to open the details page of the DFN-CERT advisory.
The following registers are available:
- Information
- General information about the DFN-CERT advisory.
- User Tags
- Assigned tags (see Chapter 8.5).
The following actions are available in the upper left corner: